“趁热打铁”出自哪里?
“趁热打铁”是从法语翻译来的成语吗?
This site utilises several optional online services that might collect information about you. By continuing visiting this site (whether or not you dismiss this dialog), you acknowledge that you accept our privacy notice.
“趁热打铁”是从法语翻译来的成语吗?
本篇收录作者在拒绝欧式汉语硬译甚至不译一些词汇时遇到的一些搞笑又(自认为)贴切的谜之翻译。
在博客中使用 BibTeX 的需求起源于一些需要引用文献的博文。例如之前的 NC¹ 属性加密 [KW19],那时候我是手工格式化参考文献的。当然,能自动化就不要手工去做,于是几个月前我开始了 BibTeX-TS——TypeScript 写的 BibTeX 解析器。现在设施已经足够完备,我可以把 alpha.bst 的实现近似翻译到 JavaScript 里,成为博客构建系统的一部分。
Just some random proposition found on Twitter.
神来之笔一般的答案背后是草稿纸上的一通狂算,考试要看的是神来之笔,但其实一通狂算里的思路更有价值。关键词:十一学校、抄答案、“注意到”、“草稿”。
WeChat has this function to distribute red envelopes of random amount of money. The natural question to ask is how to sample the amount of money each person who opens the envelope should receive.
It wasn’t until recently did I realise there are two isomorphic ways (different styles) of writing hybrid proofs. They actually correspond to the two equivalent definitions of computational indistinguishability — one based on guessing and the other based on distinguishing. Actually, I’ve been writing both kinds of proofs subconciously.
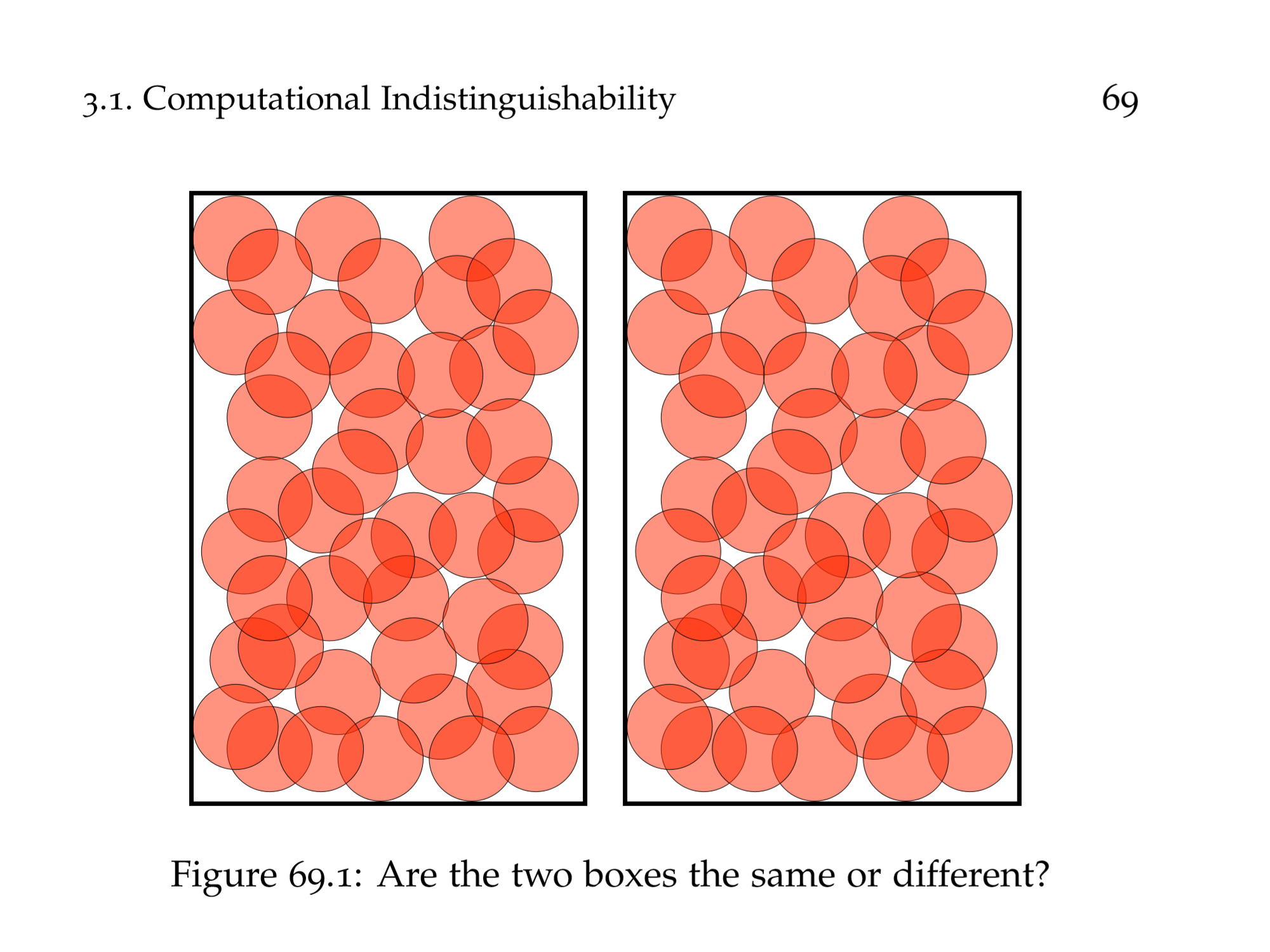
There are two asymptotically equivalent definitions of IND-CPA for secret-key encryption schemes. I think the one-challenge one makes the proof neater.
理想(ideal)是出现在抽象代数(更特别地,环论)中的一类对象,其命名很有渊源。之前我只知道这个名字来源于一位数学家研究惟一分解时引入的“理想数”(该研究的思路和一般化最终形成了现代数学语言中“理想”的定义),但是具体的细节不是很明白;最近在阅读基于格(lattice)的密码学的内容,其中提到了环上的格(ring lattice),其中提到了理想格(环的一个子集,同时满足格和理想的要求),好奇心一发不可收拾,读了一些数学历史故事,对“理想数”加深了认识,记录下来以飨观众。文章最后讨论了“理想数”这个翻译的不达意之处。
UW CSE 的 PhD 要约信中提到新入学的研究生都会获得一个免费电脑(有多种选择),我选了(标准选项里的)MacBook。这篇博文记录我初探 macOS 的事情。作为探索结果,我居然又给微软报了一个 bug!
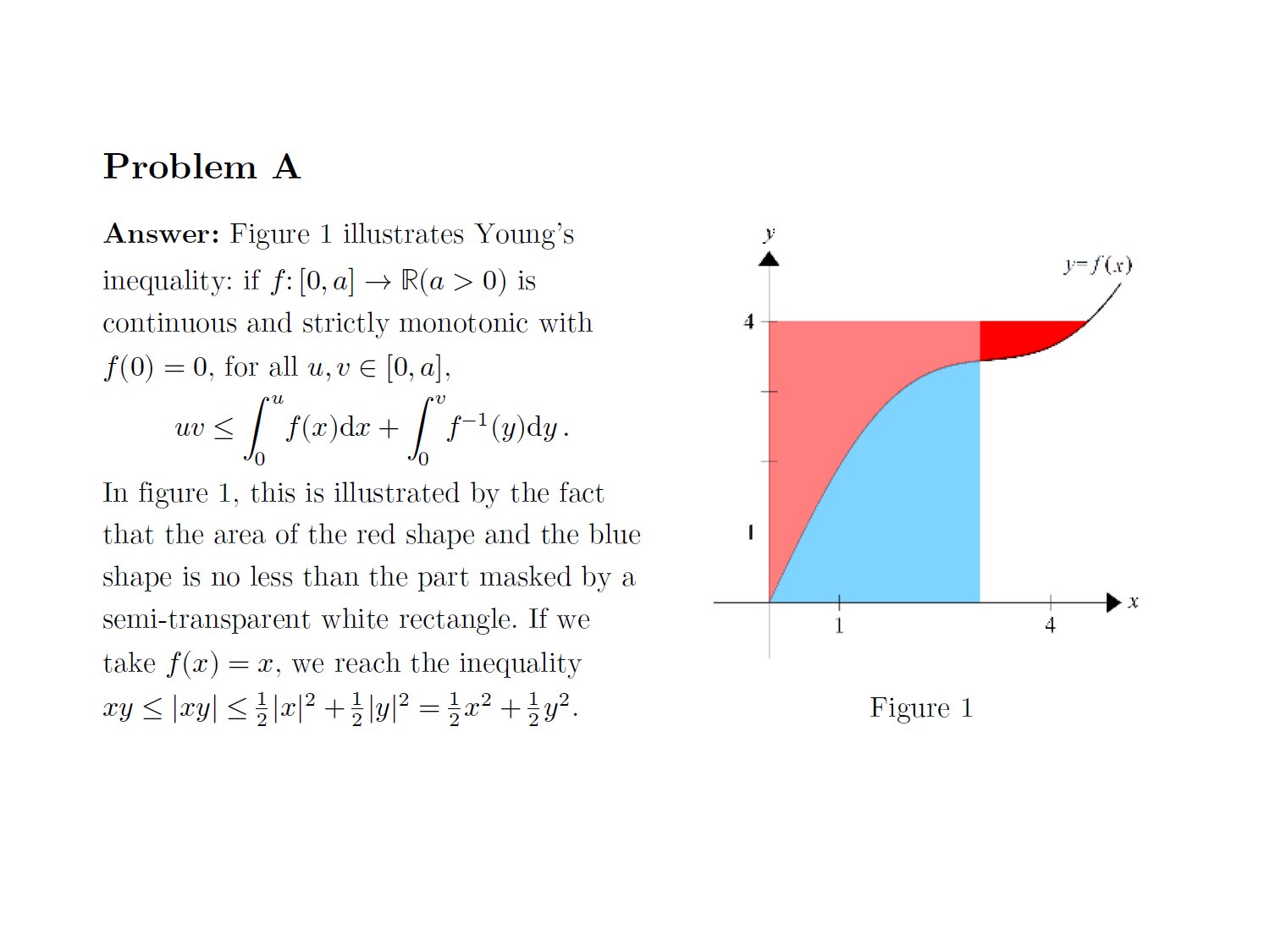
Nyuwa, the mother goddess of Chinese mythology, mends the sky according to an ancient Chinese legend. Today, Nyuwa is asked to mend the epigraph of a continuous function over an open set so that the function becomes convex. What can we say about this?

It is widely spoken that the Equation Editor of Word (OneNote / Office) is inferior and harder to use than LaTeX. While this is true for a hardcore user, a lot of people spreading the word aren’t really understanding the thing and are just parroting others. I suspect that for a lot of them, the ability to efficiently typeset beautiful mathematical formulae is limited by knowledge and carefulness. People don’t seem to care enough to learn and correctly employ the tools at hand.
I had a maths-related nightmare that (initially) was concerned about counting solutions of a linear equation modulo M with integral coefficients. Though the whole detail of the dream cannot be written down due to privacy reasons, at least I can write a simple introduction on solving this specific problem here. Update: An error in the original solution has been corrected. Another update the same day: The original solution is correct.
我感恩节期间买了 Nintendo Switch,是为了玩 Pokémon Let's Go Pikachu,也就是《口袋妖怪·黄》的重制版,为此我还配上了 Pokéball Plus(配信梦幻的精灵球形状的遥控器,也可以作计步器用)。刚刚结束一周目(登入名人堂),写篇博文记录一下。

我的博客中第一次提到《铁甲小宝》是在《清华网络碎碎念:交费死锁》,最近我又在杂乱地复习它,发现了一些有趣的事情。本篇博文介绍这些内容,并记录一些备忘知识。

A brain teaser that remains open in Yao class WeChat group, up to the time of writing of this entry. See if it interests you and if you can solve it.
一回想过去,就很容易觉得生命都过得不够充实。今天早晨偶然想要看一下自己的原来的卧室,感觉就上来了。
Someone wanted to know how to create a file that denies itself from being removed, yet found he could still remove the file even denying DELETE access from Everyone. The reason is that there is DELETE_CHILD access on its containing directory. How does this relate to ‘the directory is not empty’?
a.k.a. How to be disappointed again by UA. I was visiting New York University and Carnegie Mellon University. Flying from Beijing to New York, from New York to Pittsburgh, from Pittsburgh to Beijing via Chicago, I chose United Airlines, one that suffers from previous scandals on ‘violently reaccomodating a customer’. It turns out that their in-flight entertainment system is also torturing! This entry was written during the flight from Chicago to Beijing.
Base conversion is the conversion between notations of number, and NOT the numbers themselves. I discuss a common mistake on methods of base conversion, and a common mistake in thinking about ‘base conversion’ in computer programs.
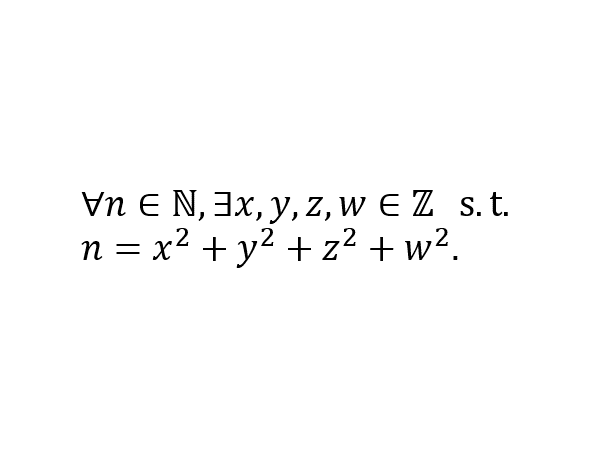
Lagrange’s four-square theorem is a beautiful result in number theory. However, to the best of my knowledge, I haven’t encountered it often in theoretical computer science. Today’s entry discusses two interesting stories related to this theorem.
I allowed myself some CHANEL products to ‘reward’ myself for the acceptance of my first cryptography paper. I also consider spending money at its best value an interesting game. A commonly-seen discount aux Galeries Lafayette Xidan (Beijing) leads to an obviously NP-complete problem. Haha!

An algorithmic imagination of how Sina Weibo could implement Frequented Visitees, a feature that gives users the serveral accounts which they visit the most often.
在 Aarhus 的密码学研究从春天到秋天一直断断续续在进行。今日传来喜讯:我们的文章已被 PKC 2018 接收。
去听习题课并不是为了听讲习题,而是为了混参与分数(虽然我相信这个课不用参与分数也可以拿很高的分)。虽然,仍然有两则有趣的见闻以飨观众。
首战 GRE 不战而败,首战 TOEFL 可以算是“凯旋归来”吧!第二次战 GRE,感觉稳了。
清华网络费用非常高!另外,曾经清华网费有死锁,因为使用了网银;后来采用了微信、支付宝,声称解决了死锁。但我今天一试,发现根本不是这样的!(已更新)

如何背叛“微软教”。7 月 24 日更新:我的一个好朋友也要换手机了!
数学文字中有很多“一般”,例如“一般地”、“不失一般性”,还有“特别地”等说法,它们的意思和日常中的“一般来说”可大不相同。
How do you localise ‘Filter’ button for Mainland China?
一篇流水账,你可以叫它“意识流”。
“回”“老家”四川对我来说是一种负担,我想回老家——回北京。
I was participating Advanced Assessment for Admission (AAA) of Tsinghua Union, passed the first phase and was interviewed by Insititute for Interdisciplinary Information Sciences of Tsinghua University. Here is a transcript of the interview.

我参加了“华约”(清华大学联盟)的自主招生(AAA,或“高水平大学自主选拔学业能力测试”)。我通过了初试并被清华大学交叉信息研究院面试。这是一份面试的转录。
