“趁热打铁”出自哪里?
“趁热打铁”是从法语翻译来的成语吗?
This site utilises several optional online services that might collect information about you. By continuing visiting this site (whether or not you dismiss this dialog), you acknowledge that you accept our privacy notice.
“趁热打铁”是从法语翻译来的成语吗?
听闻最近 Windows 10 预览版里 Alt+Tab 可以切换(新)Edge 标签页,我有一些评论想要发表。另,最近忙了很多事儿,密码学研究系列久久未更,还在计划重写博客网站,烦呀!

我最近写的一个知乎答案,简单说说我使用 OneNote 管理研究笔记一点微小的经验。🐸

Another therapy session for my Performance-Obsessive Disorder.
本篇收录作者在拒绝欧式汉语硬译甚至不译一些词汇时遇到的一些搞笑又(自认为)贴切的谜之翻译。
POD (Performance-Obsessive Disorder) is an intended pun for Plain Old Data. This entry imagines how IEnumerable<T> of .NET could be upgraded for better performance, featuring duck typing with generics.

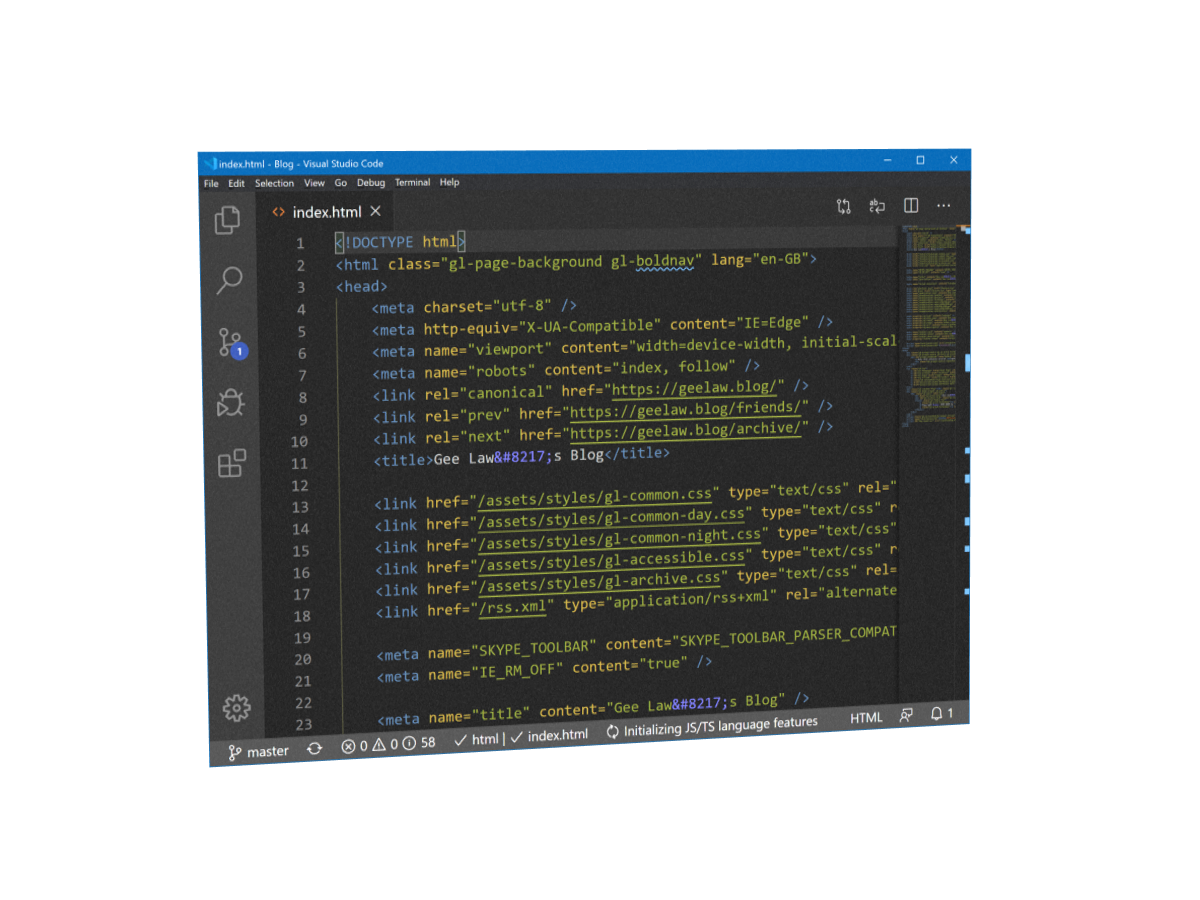
A meta-blog that keeps the trace of my blog site. The latest update reinforces the design goal of the website.
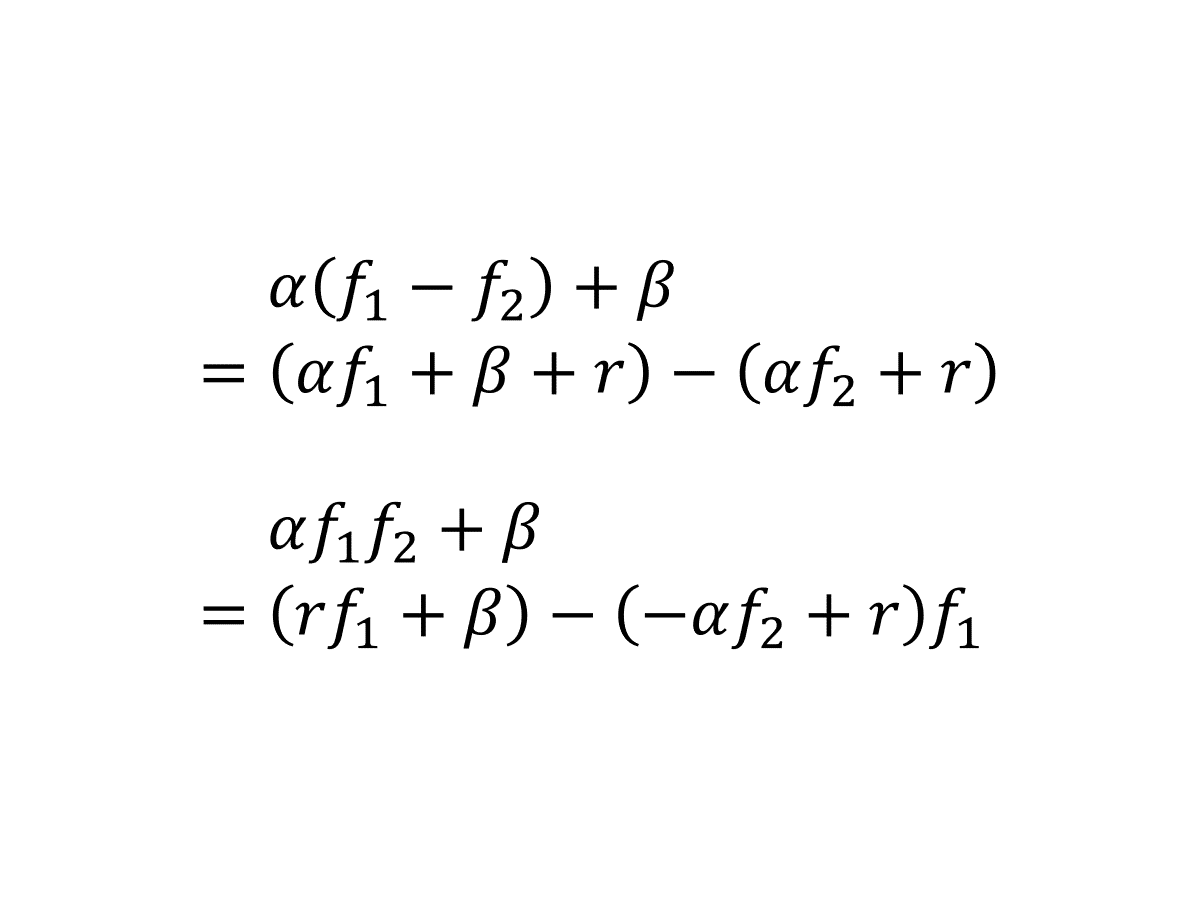
这一篇是我的 2019 年科研“属性加密”系列番外篇,记录一些关于(特殊)分段安全性的故事。这一篇的风格相较主系列更轻松活泼(肯定有人要吐槽我对“轻松活泼”的定义),比如去掉了繁复的导航按钮,减少了公式。另外这一篇也加上了“数学”的标签,大概是因为很多这里考虑的问题的密码学价值不大,更像是线性代数的游戏?
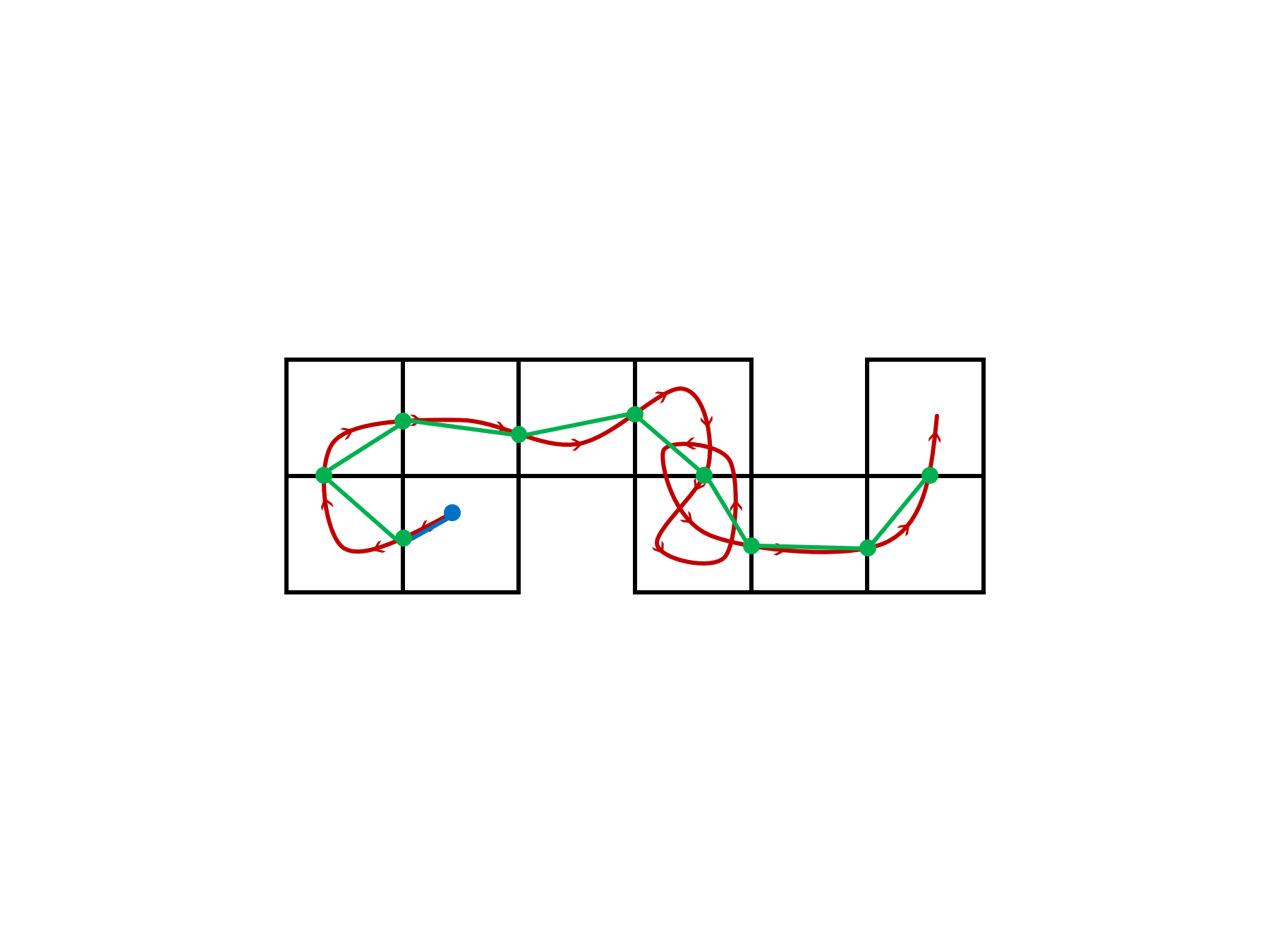
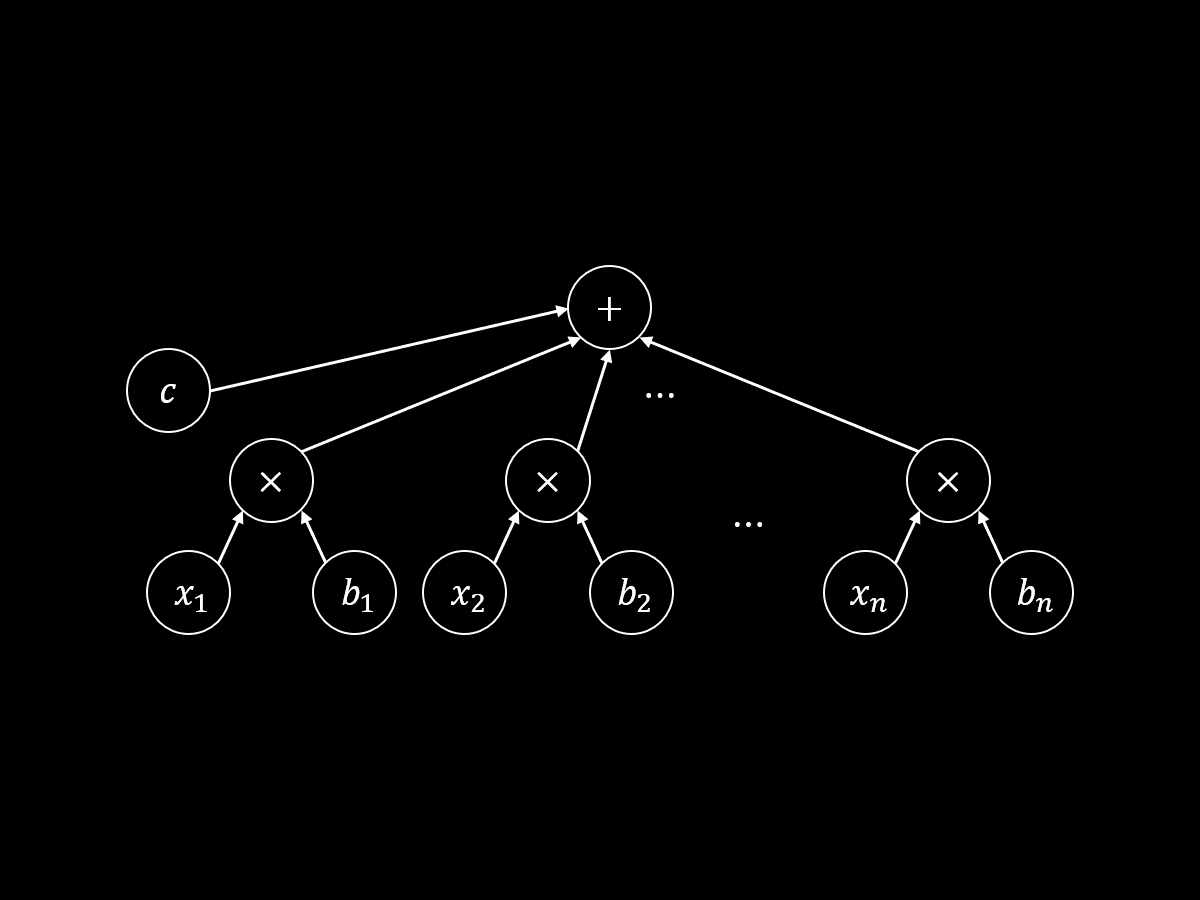
千呼万唤始出来!本文是我的 2019 年科研“属性加密”系列博文第五篇。之前一套“增加编程空间、递归模拟、树平衡化”组合拳,针对算术公式证明了 1-ABE 的适应性安全性,在这之后,我跌跌撞撞发现了最终记录在 [LL20] 里的一个关键性质:AKGS 分段安全性。这个性质大大简化了证明过程。
本文是我的 2019 年科研“属性加密”系列博文第四篇。这次揭晓上回的小悬念:解释上次的证明怎么错了,然后讨论针对算术公式的一个自然的修复思路。这个思路最终启发我发掘出了 [LL20] 中的一个关键概念,但这段故事本身并未记载在文献中,因此这一篇也肩负着重要使命:讲述文献“冰冷的美丽”背后“火热的思考”。
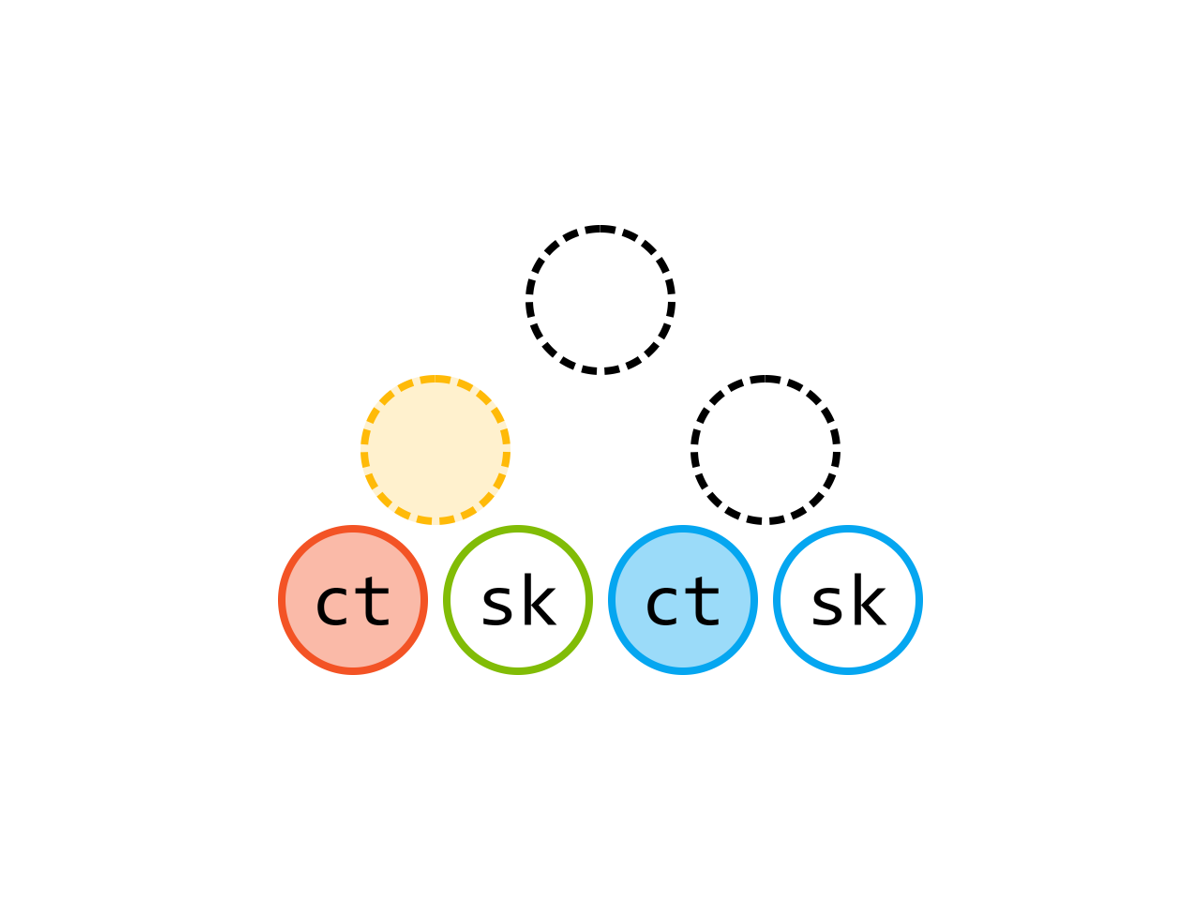
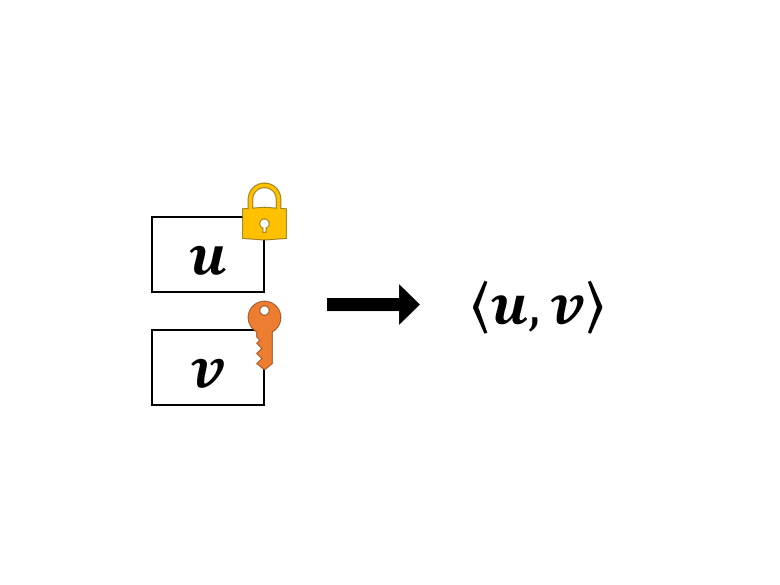
本文是我的 2019 年科研“属性加密”系列博文第三篇。在这一篇里,我将介绍 [LL20] 里构造一次性安全的属性加密方案(叫做 1-ABE)的思路——使用内积加密计算算术密钥乱码化方案的标签。本文有彩蛋!
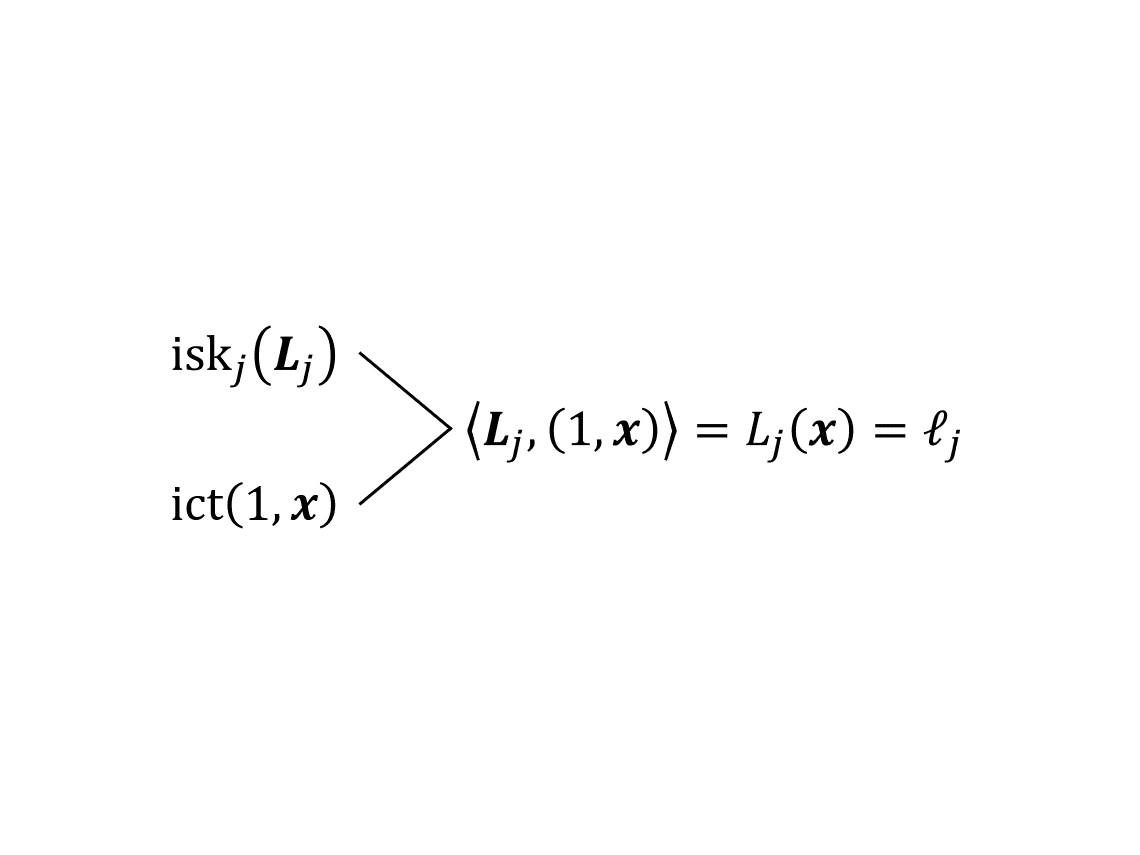
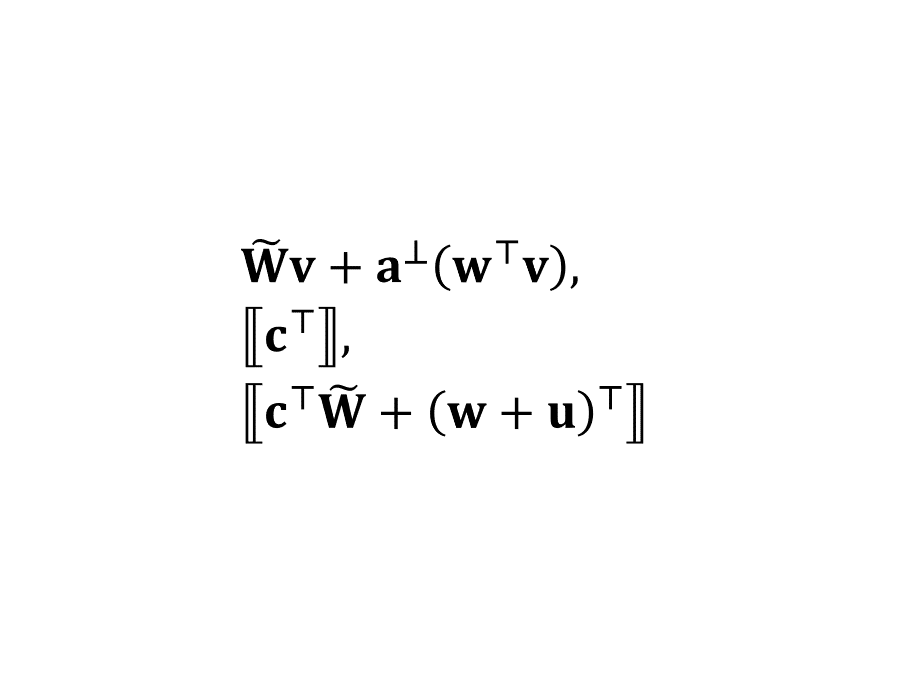
本文是我的 2019 年科研“属性加密”系列博文第二篇。在这一篇里,我将引入 [LL20] 中建立信息论意义下安全性的核心工具——算术密钥乱码化方案 (AKGS)——并给出适用于算术公式的构造。
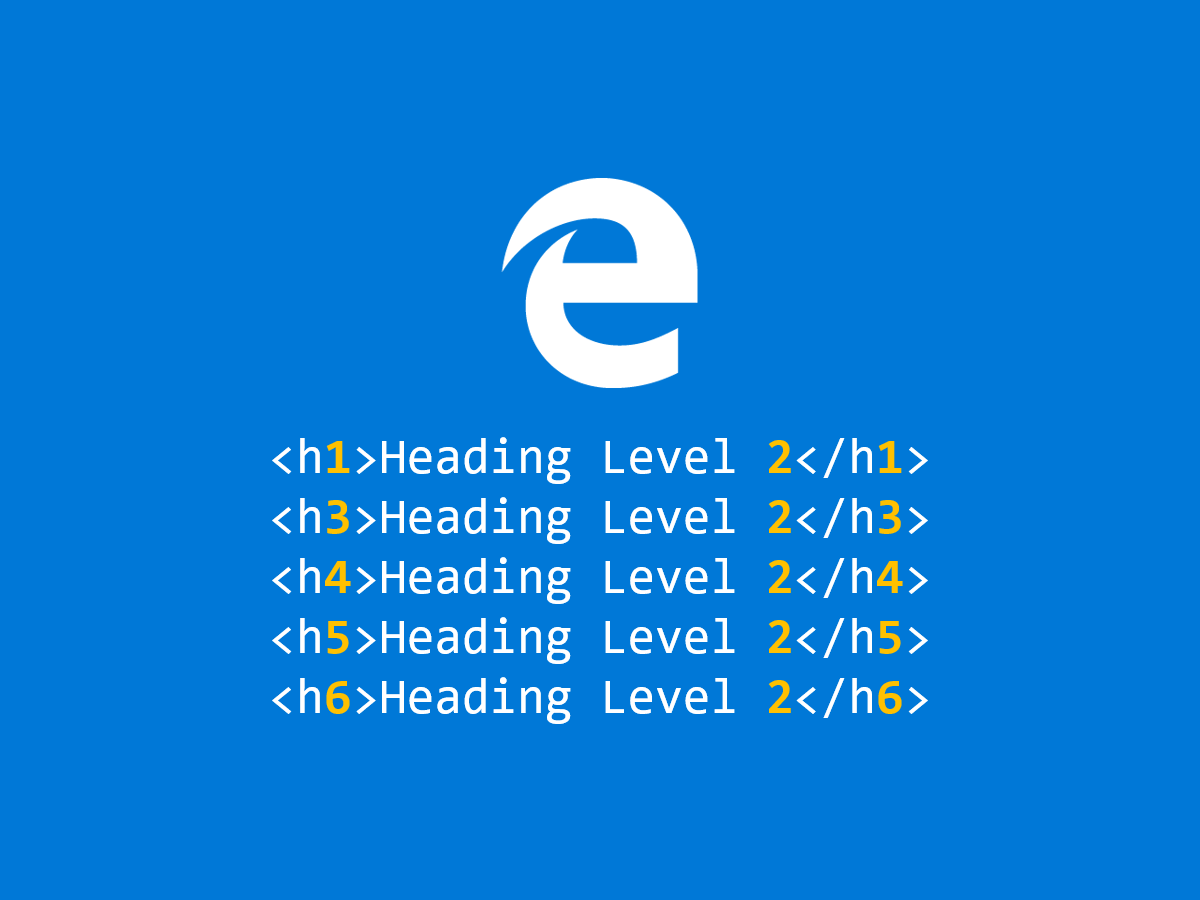
Brain-dead application of the default aria-level value (two). This problem reproduces in Microsoft Edge 44.18362.449.0 (EdgeHTML 18.18363) and Narrator for Windows 10, version 1909.
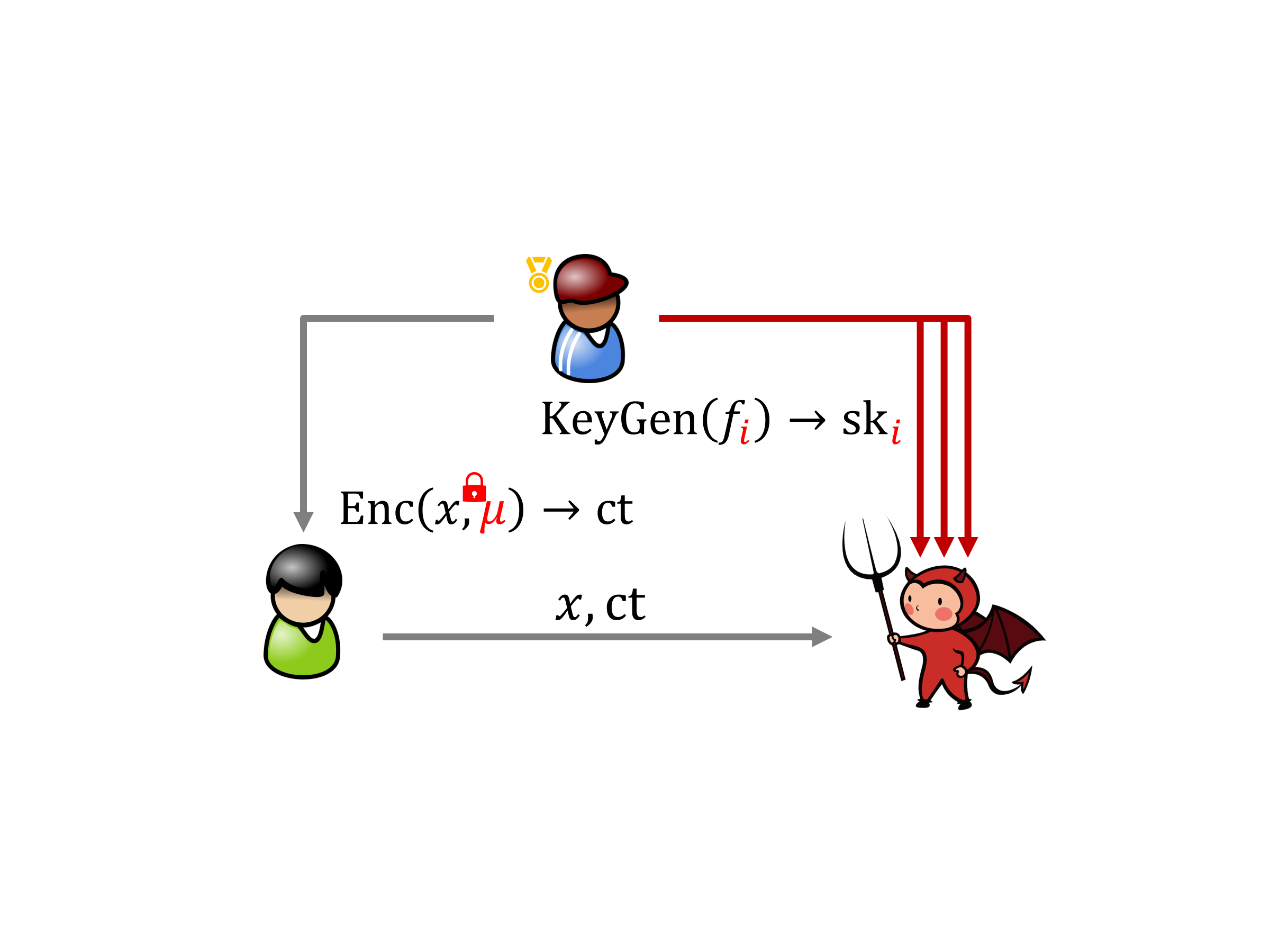
本文是我的 2019 年科研“属性加密”系列博文的首篇,该系列博文旨在用汉语介绍我和我导师的合作论文 Compact Adaptively Secure ABE from 𝑘-Lin: Beyond NC¹ and Towards NL [LL20]。在这一篇里,我将介绍属性加密的基本概念并定下一个“小目标”。
本系列旨在忠实提供 1980 版的《悲惨世界》概念版音乐剧的歌词。第二十篇也是最后一篇,记录的是 L'aveu de Valjean、Marchandage et révélation、Épilogue 的歌词。完结撒花!🎉
Some PowerPoint trick I used for preparing my Eurocrypt 2020 talk, plus a bonus.
最近在思考到底用 PowerPoint 还是 Beamer 制作我的讲座演示文稿,这里的主要顾虑是 Beamer 编写起来很累(尤其是复杂动画),而 PowerPoint 不能方便地导出根据动画分割的 PDF、幻灯片截图。网上搜索的时候在 SuperUser StackExchange 问答里发现了 PPspliT 这款神器,所以就决定是你了——PowerPoint!

Today I learnt from @Libre盖子 (Tom Li) that Windows still has the ability to not turn off the power after a system shutdown. This is so nostalgic! I haven’t seen this screen since the beginning of this century.
欢迎来到“内积加密”系列文章的后半部分,这部分科普 Lin 与 Vaikuntanathan 在 2016 年提出的内积加密算法。终于是最后一篇了,我们说说双槽内积加密。
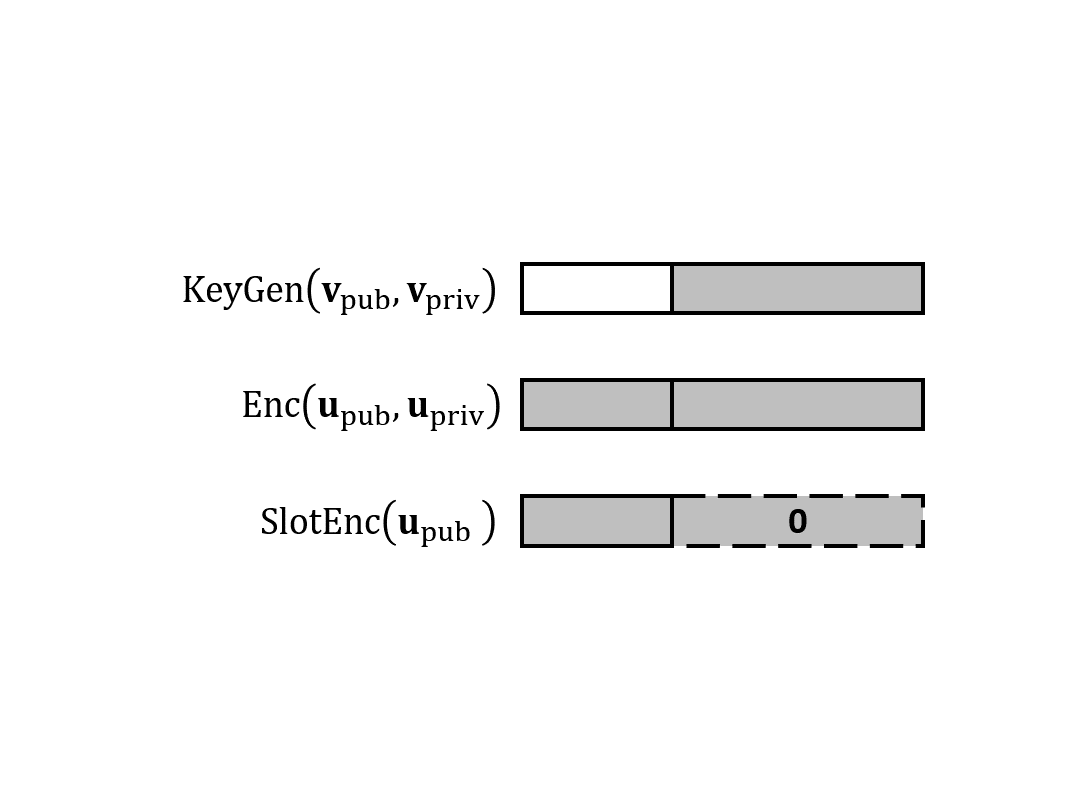
欢迎来到“内积加密”系列文章的后半部分,这部分科普 Lin 与 Vaikuntanathan 在 2016 年提出的内积加密算法。在第二篇里,我们说说如何构造具有泛函保密性的私钥 IPFE 以及它的安全性证明。(本来计划的双槽内积加密推到第三篇了。)

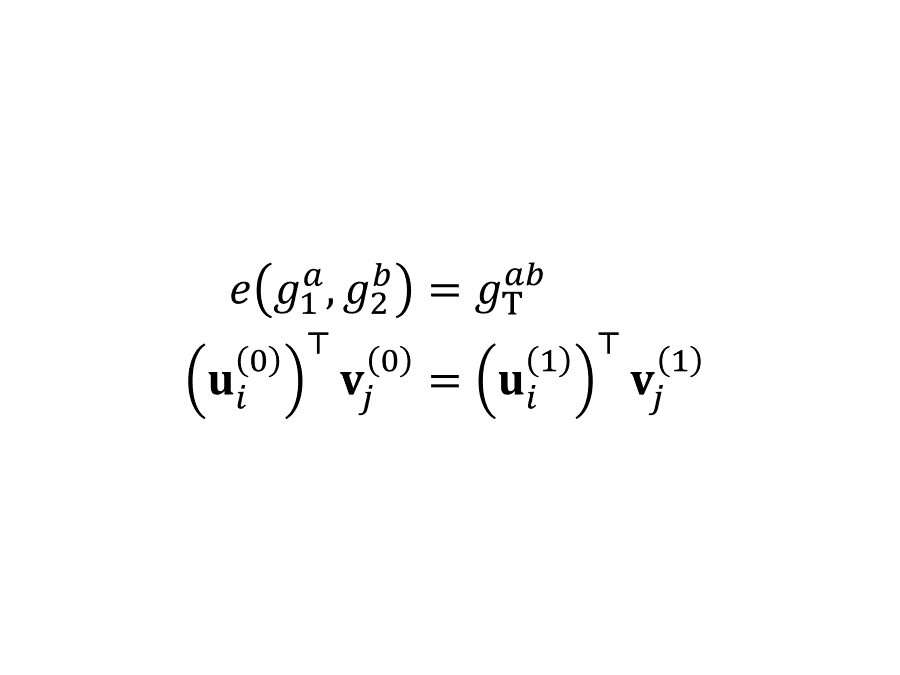
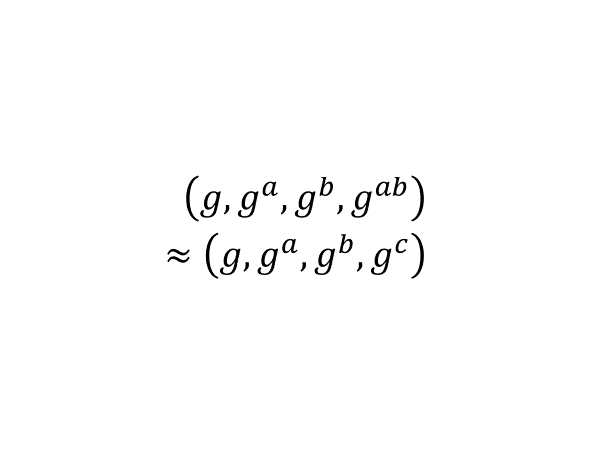
欢迎来到“内积加密”系列文章的后半部分,这部分科普 Lin 与 Vaikuntanathan 在 2016 年提出的内积加密算法。这一篇我们开始讨论前半部分未解的一个疑问:如何保护密钥里的向量?延续之前的习惯,我们先定义泛函保密性。为了构造这样的方案,我们要引入另一个工具——配对(即双线性映射)。
“内积加密”系列文章的前半部分旨在总结和科普 Agrawal、Libert、Stehlé 在 2016 年提出,Wee 在 2017 年改进,Agrawal、Libert、Monosij、Titiu 在 2020 年完善的内积加密算法。本篇是前半部分的最后一篇,叙述 ALS 公钥内积加密方案并证明它的 SIM-CPA 安全性。它的构造思想既可以理解为光滑投影哈希(也叫“哈希证明系统”)加换元法,也可以理解为双系统加密。
本系列旨在忠实提供 1980 版的《悲惨世界》概念版音乐剧的歌词。第十九篇开启第四幕(最后一幕),本篇包含 Il vivra、Marius et Monsieur Gillenormand、Le mariage 的歌词。
本系列旨在忠实提供 1980 版的《悲惨世界》概念版音乐剧的歌词。三个月后,我们迎来了久违的第十八篇,记录 Noir ou blanc 和 La mort de Gavroche 的歌词。至此,第三幕结束。
“内积加密”系列文章的前半部分旨在总结和科普 Agrawal、Libert、Stehlé 在 2016 年提出,Wee 在 2017 年改进,Agrawal、Libert、Monosij、Titiu 在 2020 年完善的内积加密算法。在这一篇里我们讨论一些针对 ALS 方案的准备知识:循环群、MDDH 假设。
Whitespace on its own does not entail a word boundary!
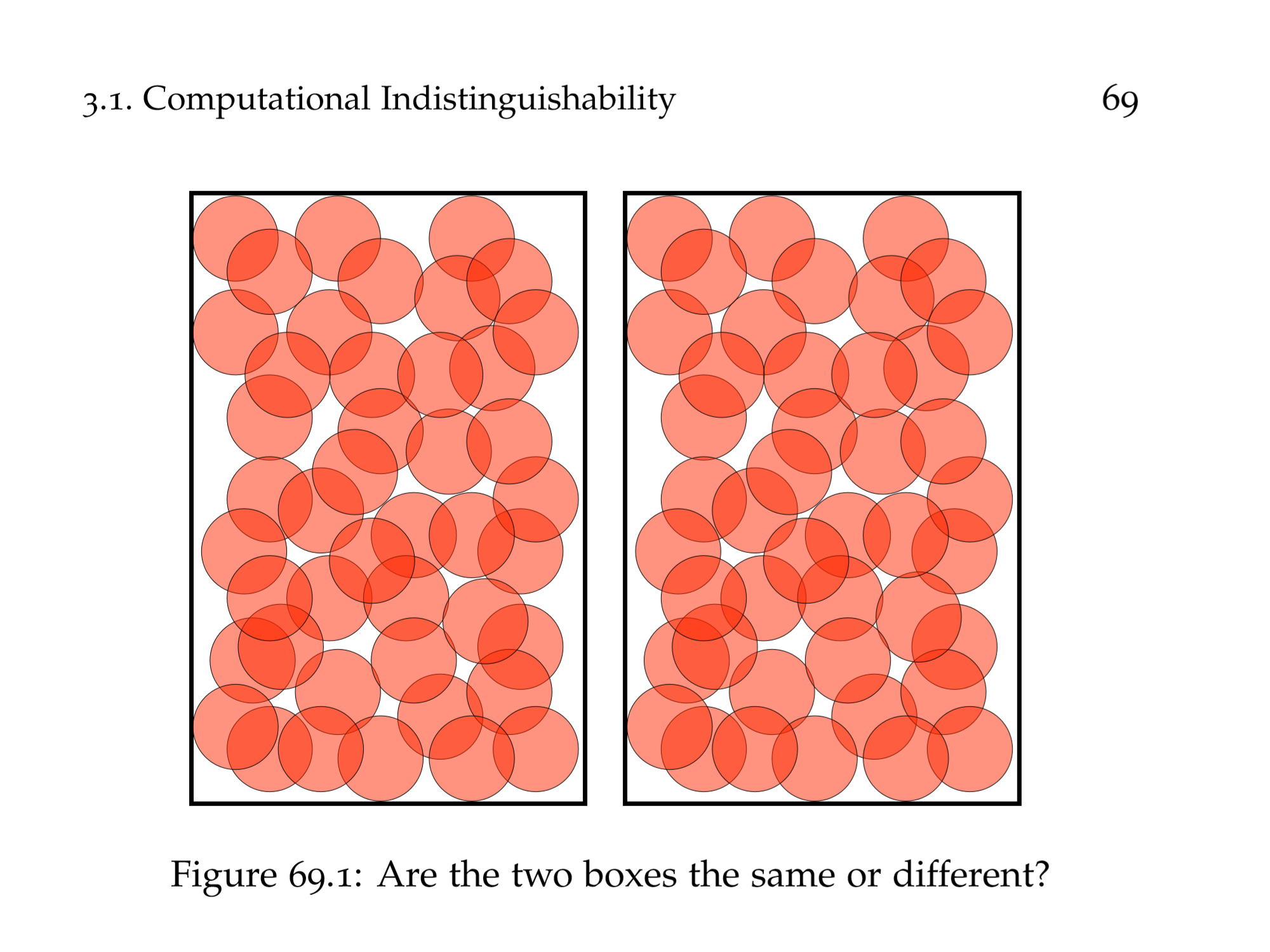
“内积加密”系列文章的前半部分旨在总结和科普 Agrawal、Libert、Stehlé 在 2016 年提出,Wee 在 2017 年改进,Agrawal、Libert、Monosij、Titiu 在 2020 年完善的内积加密算法。在这一篇里我们讨论公钥 IPFE 的语法、语义、安全性,为此我们需要引入计算意义下的不可区分性,并练习多项式时间归约和过渡证明法。
“内积加密”系列文章的前半部分旨在总结和科普 Agrawal、Libert、Stehlé 在 2016 年提出,Wee 在 2017 年改进,Agrawal、Libert、Monosij、Titiu 在 2020 年完善的内积加密算法。在这一篇里我们讨论如何用一次一密构造完美一次性模拟安全的(私钥)内积加密。
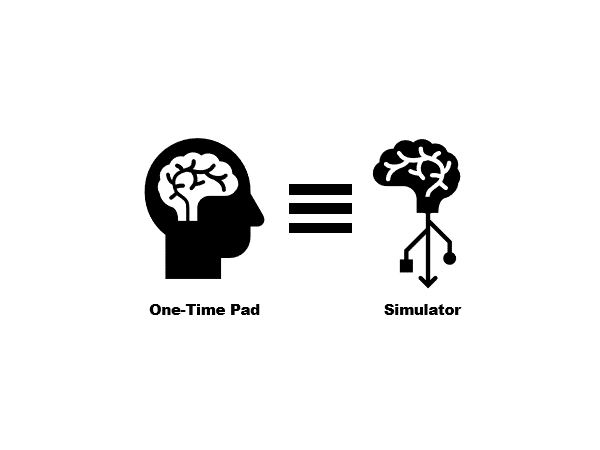
本篇博文是一系列关于内积加密的科普文章的首篇。该系列文章的前半部分旨在总结和科普 Agrawal、Libert、Stehlé 在 2016 年提出,Wee 在 2017 年改进,Agrawal、Libert、Monosij、Titiu 在 2020 年完善的内积加密算法。在这一篇里我们讨论内积加密、完美保密性和完美模拟安全性的定义,并初步讨论这两种安全性之间的关系。
在博客中使用 BibTeX 的需求起源于一些需要引用文献的博文。例如之前的 NC¹ 属性加密 [KW19],那时候我是手工格式化参考文献的。当然,能自动化就不要手工去做,于是几个月前我开始了 BibTeX-TS——TypeScript 写的 BibTeX 解析器。现在设施已经足够完备,我可以把 alpha.bst 的实现近似翻译到 JavaScript 里,成为博客构建系统的一部分。
The obvious answer to this little geometry puzzle is 3/√2, but can you prove it?
Microsoft Edge (Chromium) can pin websites to Taskbar in an undocumented way. I did some observation fun and this entry tells you how to programmatically pin/unpin Shortcuts to/from Taskbar (as of 1909). You should not abuse this knowledge.
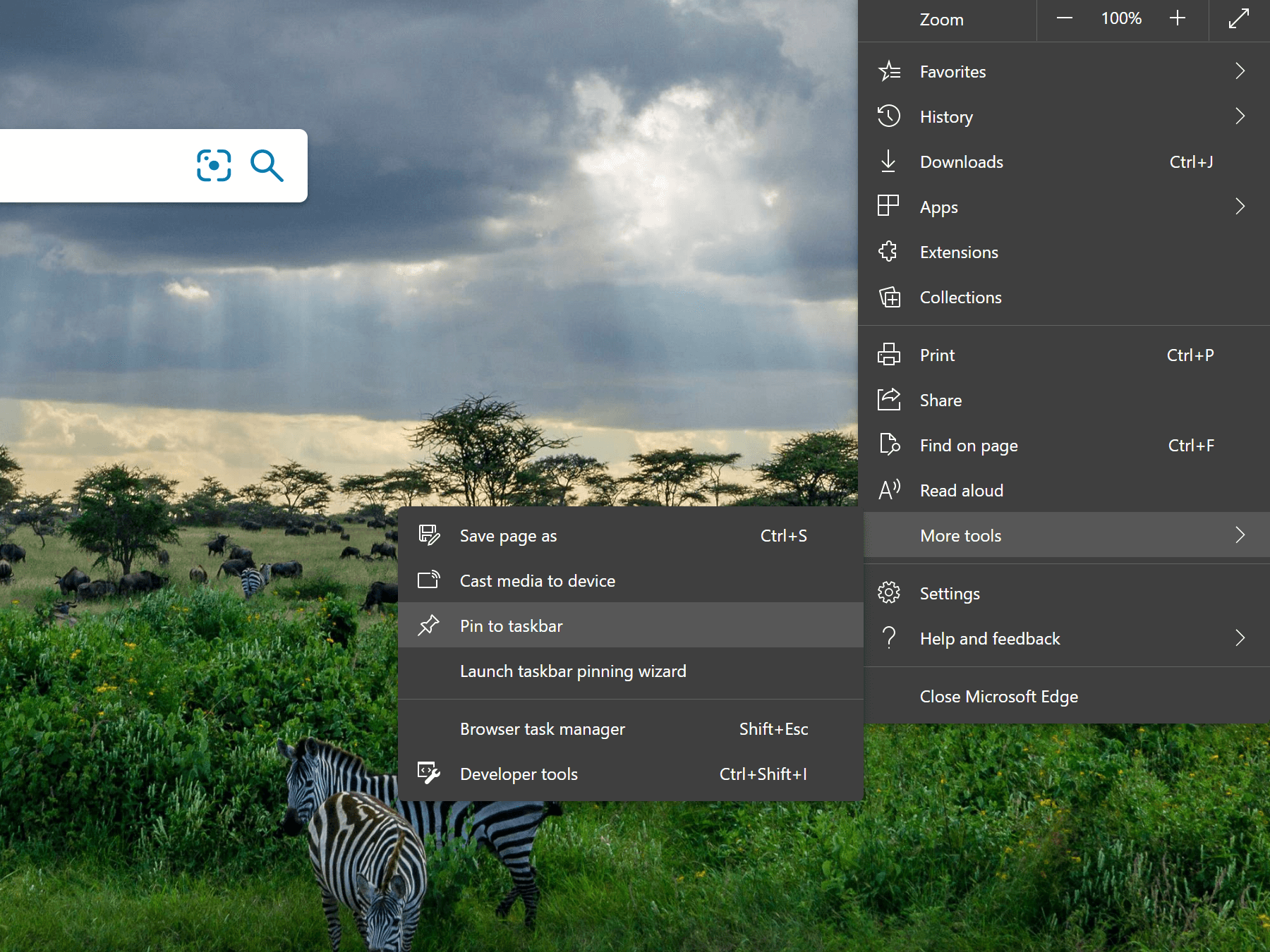
Since Edge (Chromium) has its first stable release available, I decided to give it a try, and I am particularly interested in how it behaves under High Contrast mode and what its Live Tiles look like. Aside from being unsatisfied by the current implementation of the two, I got into much larger trouble by installing the stable version of Edge (Chromium), especially via MSI!

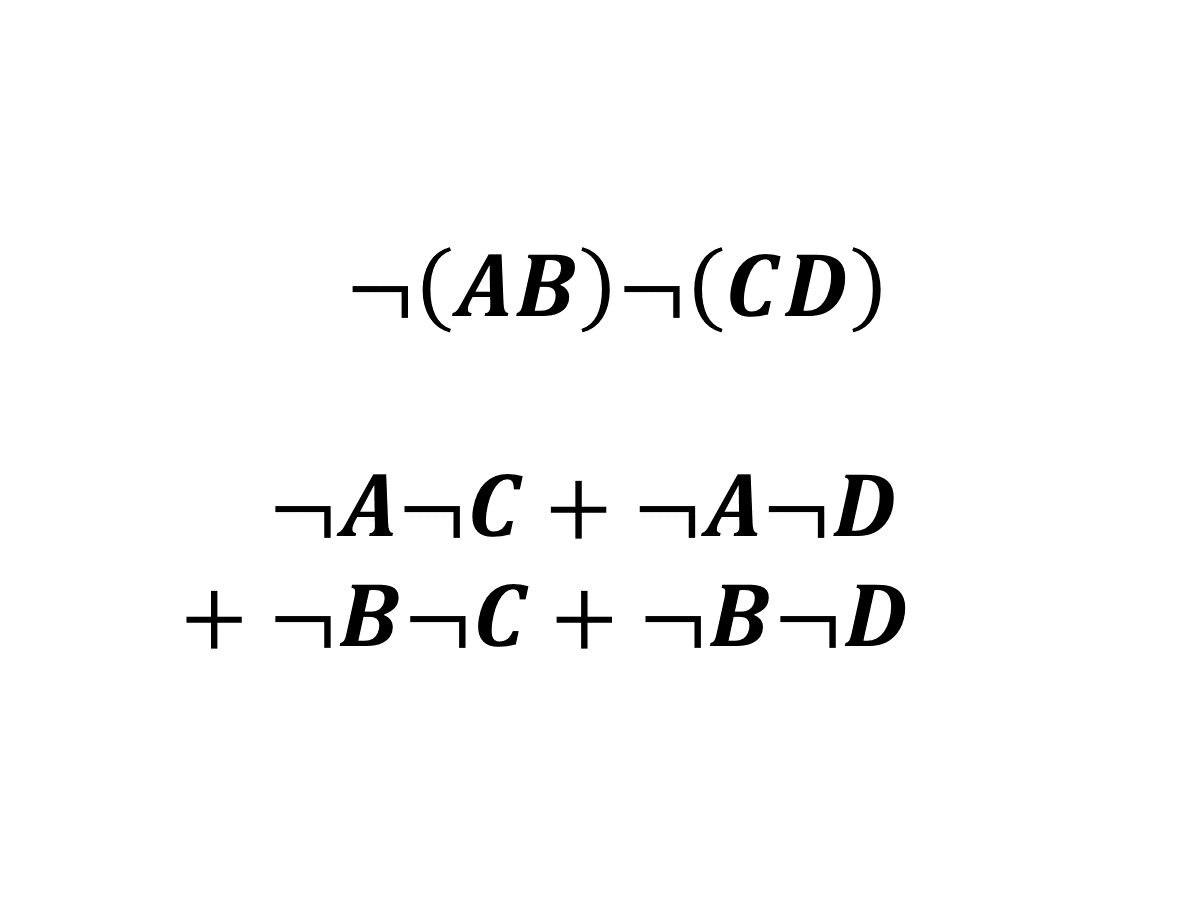
Just some random proposition found on Twitter.
最近有网友发现自己的 Windows 锁屏壁纸被修改成了百度云管家的广告。(一开始大家觉得是百度云管家乱搞,后来发现实际上是联想的 OEM 软件乱搞。)无论怎样,这说明一些软件用正常方式运行总让人不够放心,采取措施隔离一些 app 很有必要。一些网友提出可以给 app 准备一个专门的虚拟机,不过这有点大炮打蚊子了,其实可以用 Windows 的多用户和“以其他用户身份运行”解决。这个方法适用于很多 Windows 桌面 app。

Notes for UMich EECS 598 (2015) are for Lattices in Cryptography virtually instructed by Chris Peikert (i.e., I taught myself using resources made available by him). This entry is for homework 3, homework 4 and lecture note 5.
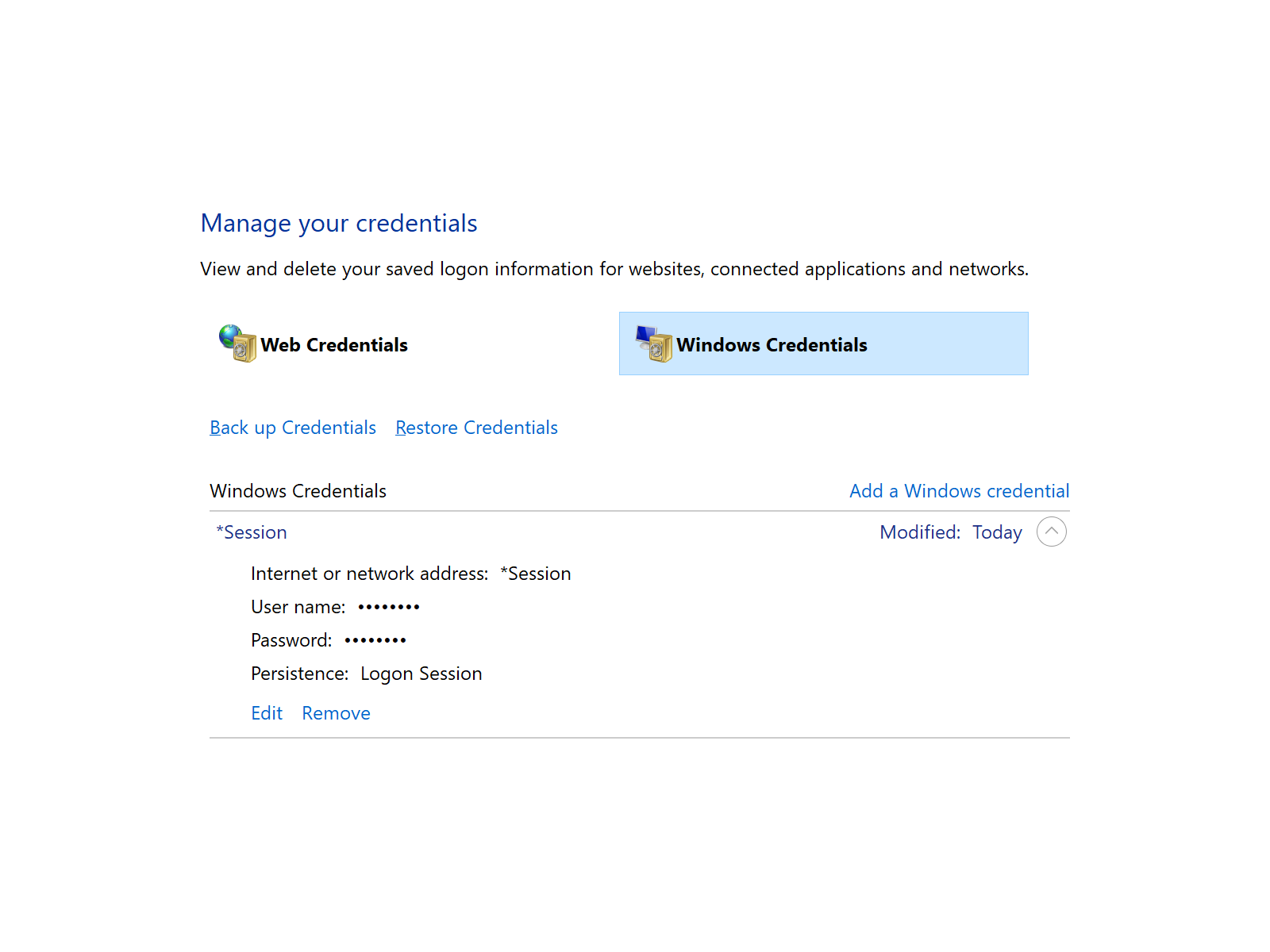
I was on eduroam (or any WPA2-Enterprise Wi-Fi network). I wanted to install UW CSE printers (or access any other domain resources). I got ‘Logon failure: the user has not been granted the requested logon type at this computer.’ Here’s why it happens and how to avoid it.
Notes for UMich EECS 598 (2015) are for Lattices in Cryptography virtually instructed by Chris Peikert (i.e., I taught myself using resources made available by him). This entry is for homework 2.
Notes for UMich EECS 598 (2015) are for Lattices in Cryptography virtually instructed by Chris Peikert (i.e., I taught myself using resources made available by him). This entry is for lecture 4, Coppersmith, cryptanalysis.
Notes for UMich EECS 598 (2015) are for Lattices in Cryptography virtually instructed by Chris Peikert (i.e., I taught myself using resources made available by him). This entry is for homework 1.
Notes for UMich EECS 598 (2015) are for Lattices in Cryptography virtually instructed by Chris Peikert (i.e., I taught myself using resources made available by him). This entry is for lecture 3, LLL, Coppersmith.
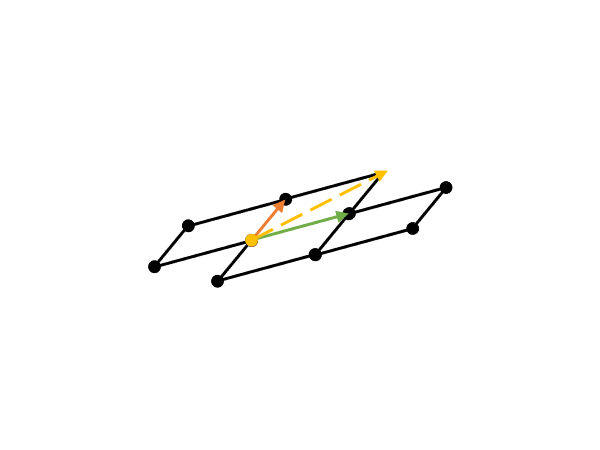
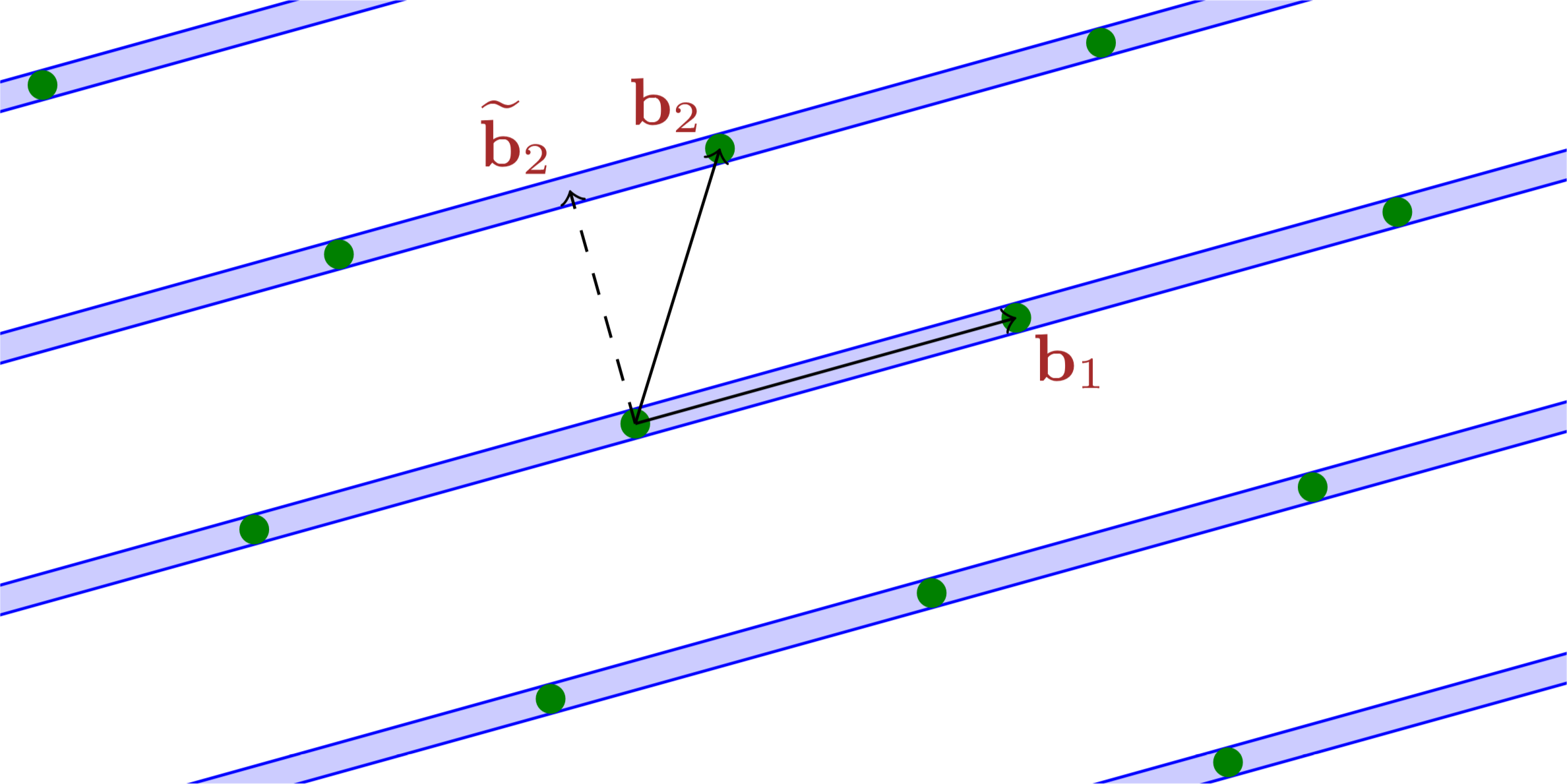
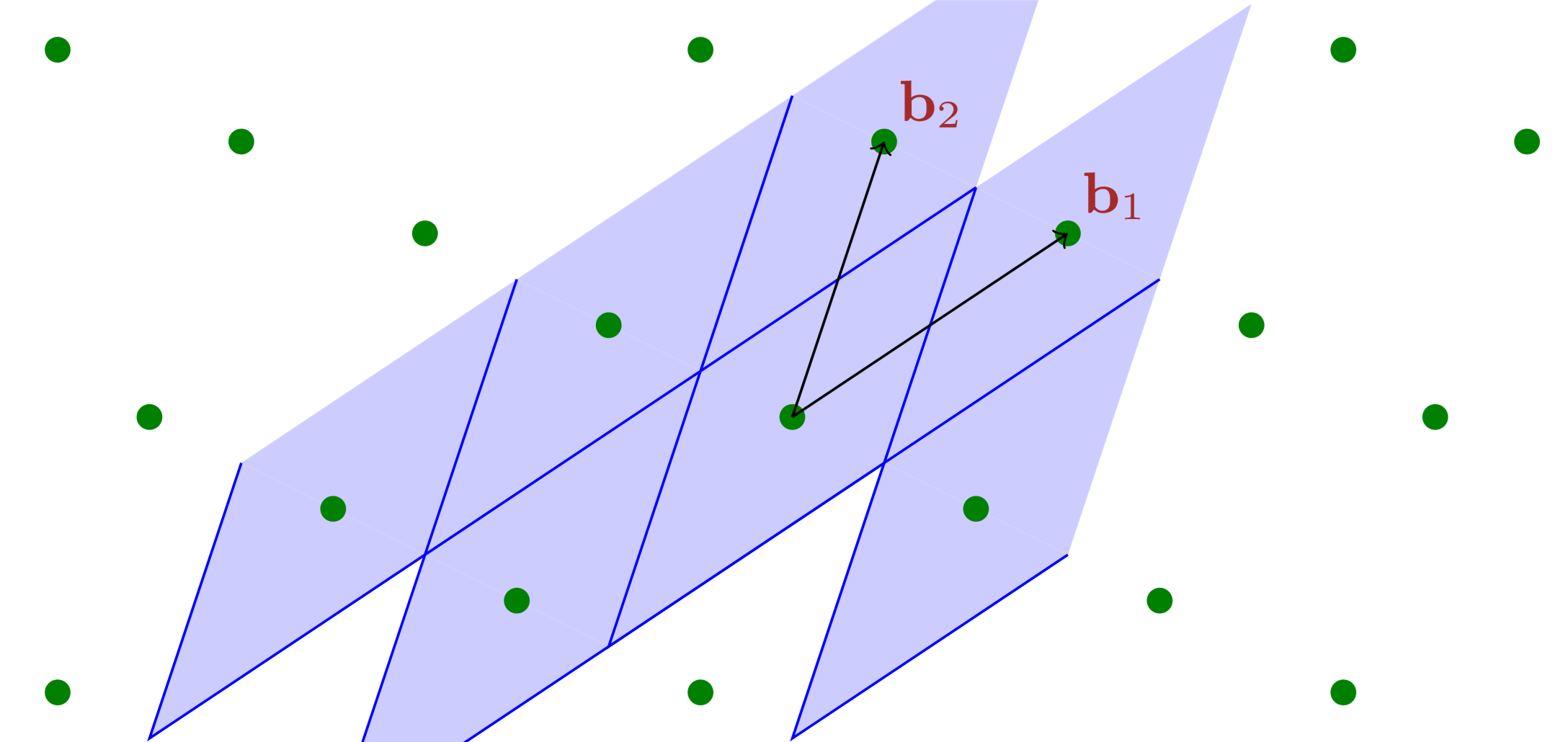
Notes for UMich EECS 598 (2015) are for Lattices in Cryptography virtually instructed by Chris Peikert (i.e., I taught myself using resources made available by him). This entry is for lecture 2, SVP, Gram–Schmidt, LLL.
Notes for UMich EECS 598 (2015) are for Lattices in Cryptography virtually instructed by Chris Peikert (i.e., I taught myself using resources made available by him). This entry is for lecture 1, mathematical background.
Finally, this happened to me… I ran something close to ‘rm -rf ~’ by accident, and pressed Ctrl+C as soon as I realised something wrong was going on. This blog entry is about how I recovered from this mistake.

本系列旨在忠实提供 1980 版的《悲惨世界》概念版音乐剧的歌词。第十七篇记录了 La nuit de l'angoisse 和 Valjean à la barricade 的歌词。此外,我还发现 ina.fr 有一段 Valjean chez les Thénardier 和 La valse de la fourberie 的录像(可免费观看),以及一个付费视频可能包含更多现场录像。
You might expect PowerShell ConvertTo-Json cmdlet produce a JSON representation of a ‘POD’ that can be parsed (in particular, by ConvertFrom-Json cmdlet) into a POD object that equals to the previously serialised one. However, this is not true for many cases, the most surprising among which are double-precision numbers.
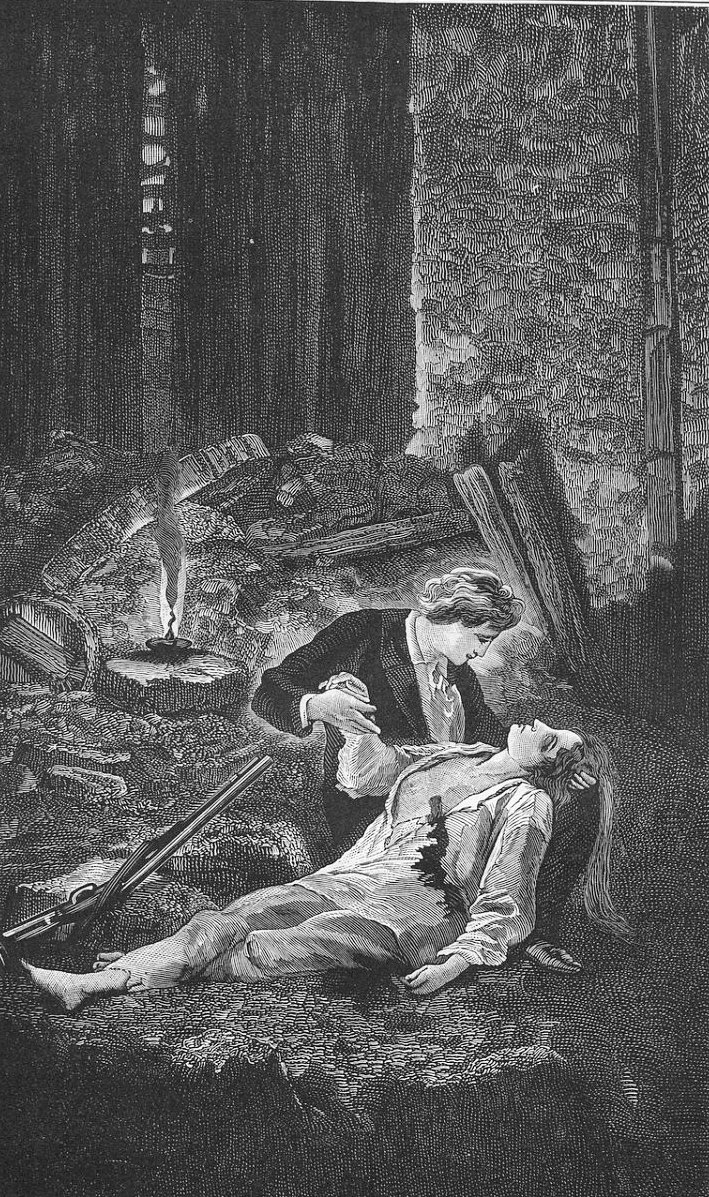
本系列旨在忠实提供 1980 版的《悲惨世界》概念版音乐剧的歌词。第十六篇记录了 Javert démasqué、Le retour d'Éponine 和 Ce n'est rien 的歌词,情节跌宕起伏,先是革命者捉住了间谍 Javert,紧接着就是 Éponine 为爱牺牲。
神来之笔一般的答案背后是草稿纸上的一通狂算,考试要看的是神来之笔,但其实一通狂算里的思路更有价值。关键词:十一学校、抄答案、“注意到”、“草稿”。
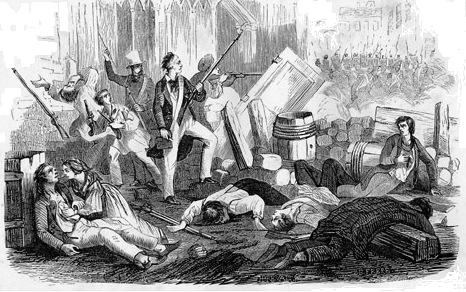
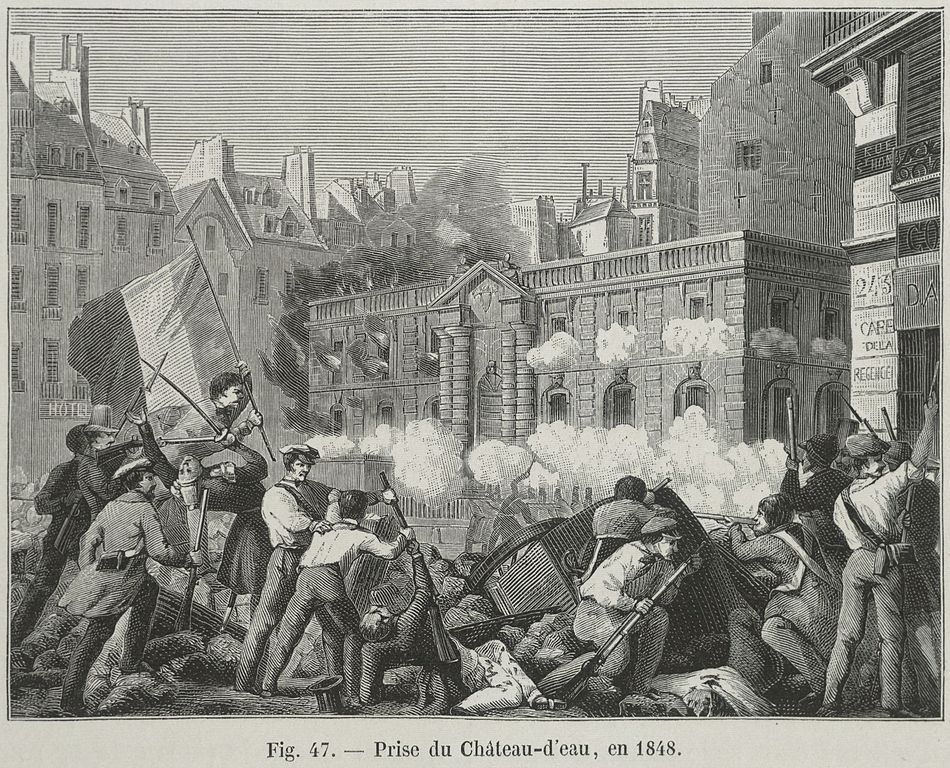
本系列旨在忠实提供 1980 版的《悲惨世界》概念版音乐剧的歌词。第十五篇起是第三幕,这一篇记录了 Construction de la barricade 和 La faute à Voltaire 的歌词。另外,系列中本篇首次启用新注解模式。
WeChat has this function to distribute red envelopes of random amount of money. The natural question to ask is how to sample the amount of money each person who opens the envelope should receive.
本系列旨在忠实提供 1980 版的《悲惨世界》概念版音乐剧的歌词。第十四篇记录的是 L'attaque de la rue Plumet 和 Demain(对应于之后版本里的 One Day More 和 Le grand jour)的歌词。第二幕完结撒花!

It wasn’t until recently did I realise there are two isomorphic ways (different styles) of writing hybrid proofs. They actually correspond to the two equivalent definitions of computational indistinguishability — one based on guessing and the other based on distinguishing. Actually, I’ve been writing both kinds of proofs subconciously.
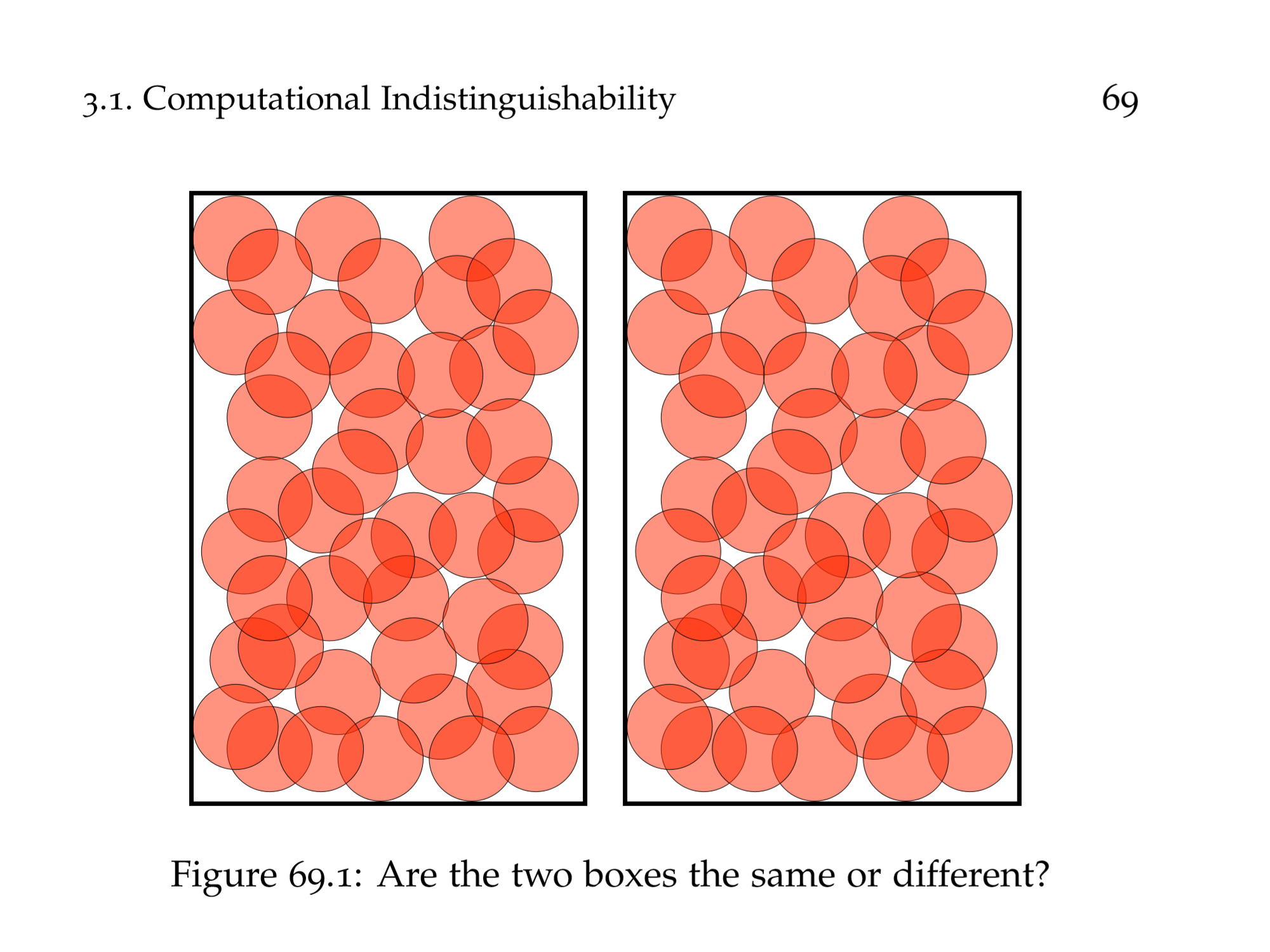
I learnt how to write uniform hybrid reductions in my rudimentary cryptography course, which are beasty beauties that wrap an adversary, trying break each of the many underlying cryptographic assumptions simultaneously. However, those constructions are less easy to write and read than using the transitivity of computational indistinguishability up to polynomially many times. The latter involves writing out the (perhaps polynomially many) hybrids and arguing that adjacent hybrids are indistinguishable. I also learnt non-uniform reductions, noticeably the technique to only work with deterministic adversaries. I’m writing a proof using hybrid argument lately, and I asked my advisor about whether I should write the beast or just the hybrids…
There are two asymptotically equivalent definitions of IND-CPA for secret-key encryption schemes. I think the one-challenge one makes the proof neater.
本系列旨在忠实提供 1980 版的《悲惨世界》概念版音乐剧的歌词。第十三篇记录的是 Voilà le soir qui tombe !、L'un vers l'autre 和 Le cœur au bonheur 的歌词,这一段是经典的白学现场。

Kowalczyk 和 Wee 在 EUROCRYPT 2019(欧密会)上发表的文章 Compact Adaptively Secure ABE for NC¹ from 𝑘-Lin 可以说是彻底解决了 NC¹ 访问策略的属性加密问题。我在最近的密码学读书会上将讲述该文,这篇博文算是我用母语对该文章的总结(感觉我脑内思考语言仍然是汉语),也算是在中文密码学社区里传播知识。
![[KW19] 标准假设下适用于 NC¹ 策略的紧凑、适应性安全的属性加密](/entries/kw19-abe-nc1/assets/hero.png)
This just struck me. Of course, it has been carefully studied by computer scientists.
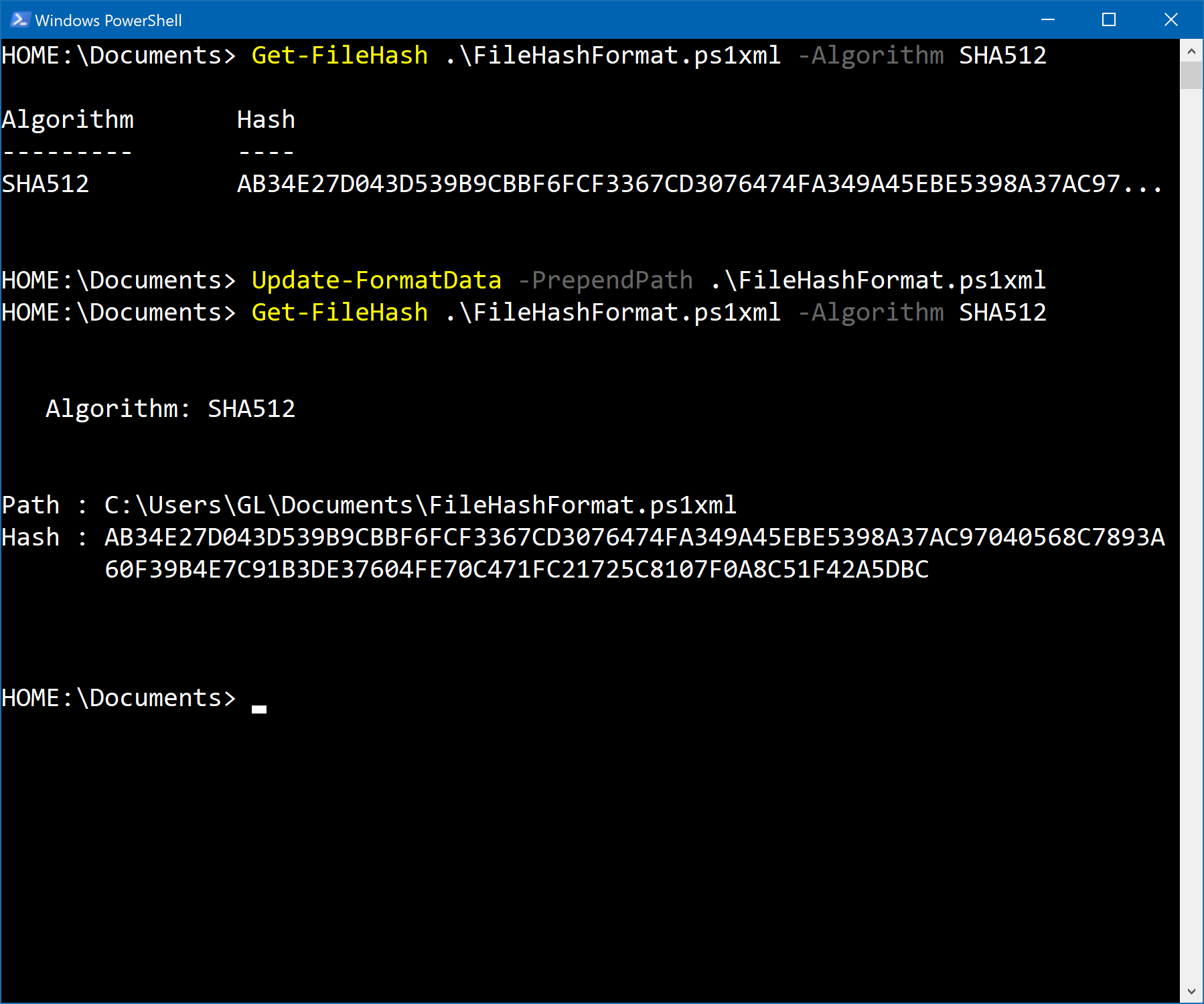
It is not the cmdlet that truncated the string. It’s the formatting. By the way, you can change the default if you want, and it’s all documented.
本系列旨在忠实提供 1980 版的《悲惨世界》概念版音乐剧的歌词。第十二篇记录的是 Te souviens-tu du premier jour ?、Cosette : Dans la vie 和 Marius : Dans la vie 的歌词,这一段是 Marius 在 Éponine 的帮助下找到了 Cosette 的住处,两个互相暗恋的人终于重逢的情节。
理想(ideal)是出现在抽象代数(更特别地,环论)中的一类对象,其命名很有渊源。之前我只知道这个名字来源于一位数学家研究惟一分解时引入的“理想数”(该研究的思路和一般化最终形成了现代数学语言中“理想”的定义),但是具体的细节不是很明白;最近在阅读基于格(lattice)的密码学的内容,其中提到了环上的格(ring lattice),其中提到了理想格(环的一个子集,同时满足格和理想的要求),好奇心一发不可收拾,读了一些数学历史故事,对“理想数”加深了认识,记录下来以飨观众。文章最后讨论了“理想数”这个翻译的不达意之处。
本系列旨在忠实提供 1980 版的《悲惨世界》概念版音乐剧的歌词。第十一篇记录的是 À la volonté du peuple 的歌词。这一曲歌词很短,但是没有和后面的曲目在一起,是因为我觉得接下来的几曲的话题和这首不太搭,而且这首这么知名,故单独成篇。本篇也特别包含了 1991 版本的此曲。

When you paste a URL of a YouTube video into OneNote, the cover image and the title are fetched by OneNote, the text of the link becomes the title, and an online video object (with the cover image) is inserted following the link. How can you disable this feature?
It doesn’t. Don’t invent a global conspiracy too early.
本系列旨在忠实提供 1980 版的《悲惨世界》概念版音乐剧的歌词。第十篇记录的是 Rouge et noir 和 Les amis de l'ABC 的歌词,革命的剧情要开始了。
本系列旨在忠实提供 1980 版的《悲惨世界》概念版音乐剧的歌词。第九篇记录的是 La misère (reprise) 和 L'attaque 的歌词,这两首都仅出现在现场录音中。很期待下一次——终于要开始热血的部分了。

本系列旨在忠实提供 1980 版的《悲惨世界》概念版音乐剧的歌词。距离上次更新(第七篇)已经过去了 9 个月,原因除了变忙没时间精听之外,还有难度的飙升。第八篇就一首,第二幕第一曲 Donnez, donnez,非常长,而且有很多市井话。这一篇开始封面图会根据本篇曲目选择。

Ever since I used Windows NT (for me, the first Windows NT I used is Windows XP), I’ve been familiar with the importance of Ctrl+Alt+Delete. The combination is known as the secure attention sequence for Windows. In an uninfected copy of Windows, the sequence is handled exclusively by Windows, and is used to thwart trojan dialogs luring users’ credentials. Requiring SAS before Welcome Screen is a quite usable security feature. However, it is not the case for Credential User Interface.
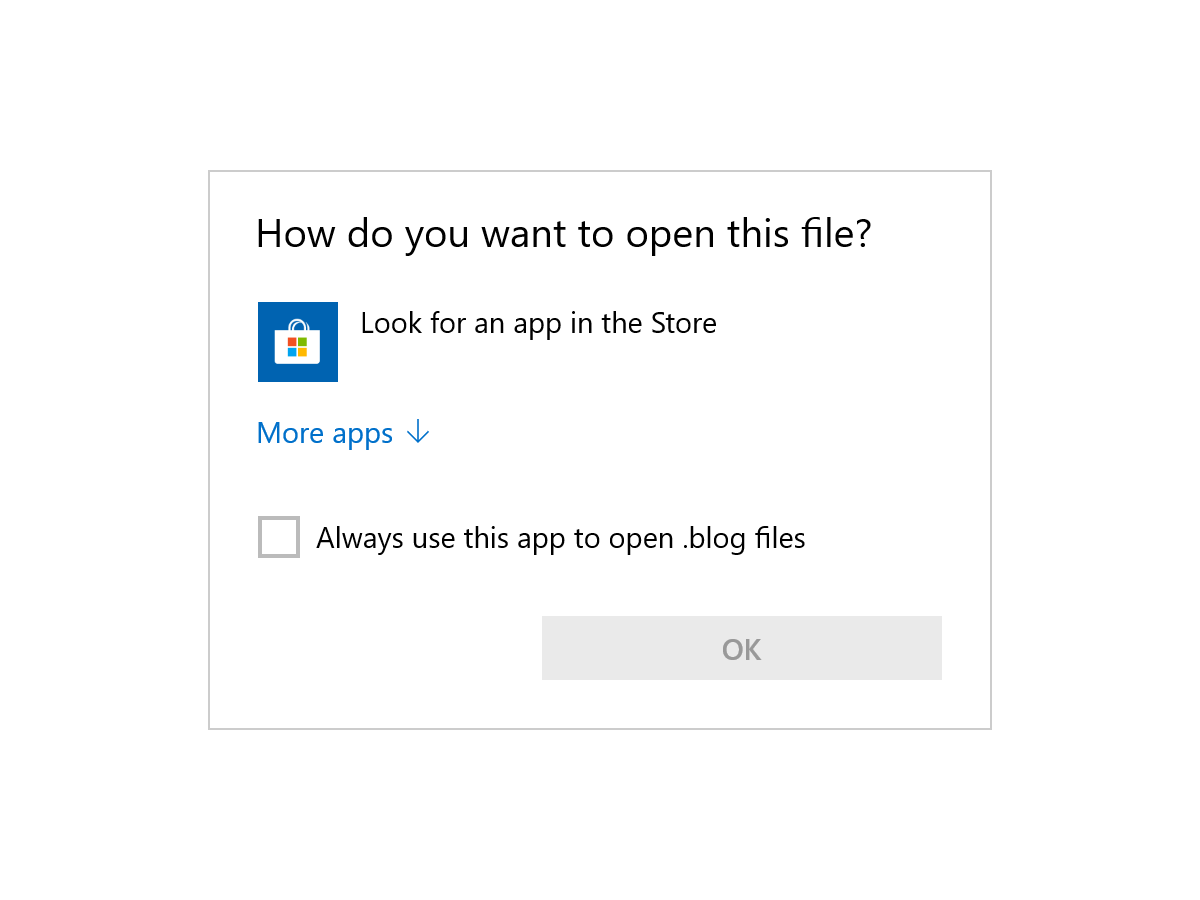
——原标题《Windows 文件关联略解》。上古时期一些乱七八糟的软件喜欢瞎搞文件关联,现在情况好多了。这篇博客简略讲述 Windows shell 的文件关联机制(不涉及 URL 协议关联)。这篇文章并不是 Microsoft 官方文档,一切请以官方文档为准。本篇的代码在 GitHub 上可见。
《化学是你,化学是我》的英文名是 Chemistry is you, chemistry is me,歌词作者是时任北京大学校长周其凤,歌曲一经发布即获广泛关注并被评论为“天雷滚滚”、《忐忑》后的新神曲。我,化学竞赛的逃兵,突然想起来这首歌,并且之前听过它的英文版,既然是“天雷滚滚”,自然比较配惊蛰,就写这么一篇吧。

PowerShell 在众 shell 中最突出的特色就是面向对象;然而,世界上还有很多命名是专为字节流管道设计的(兼容性大坑)。PowerShell 对待字节流管道那是十分 nasty!我写的这个小工具可以在对象和字节流之间做完美的润滑。更新:Aloxaf 实现了 Linux 版本的 Use-RawPipeline,起名 Use-PosixPipeline。
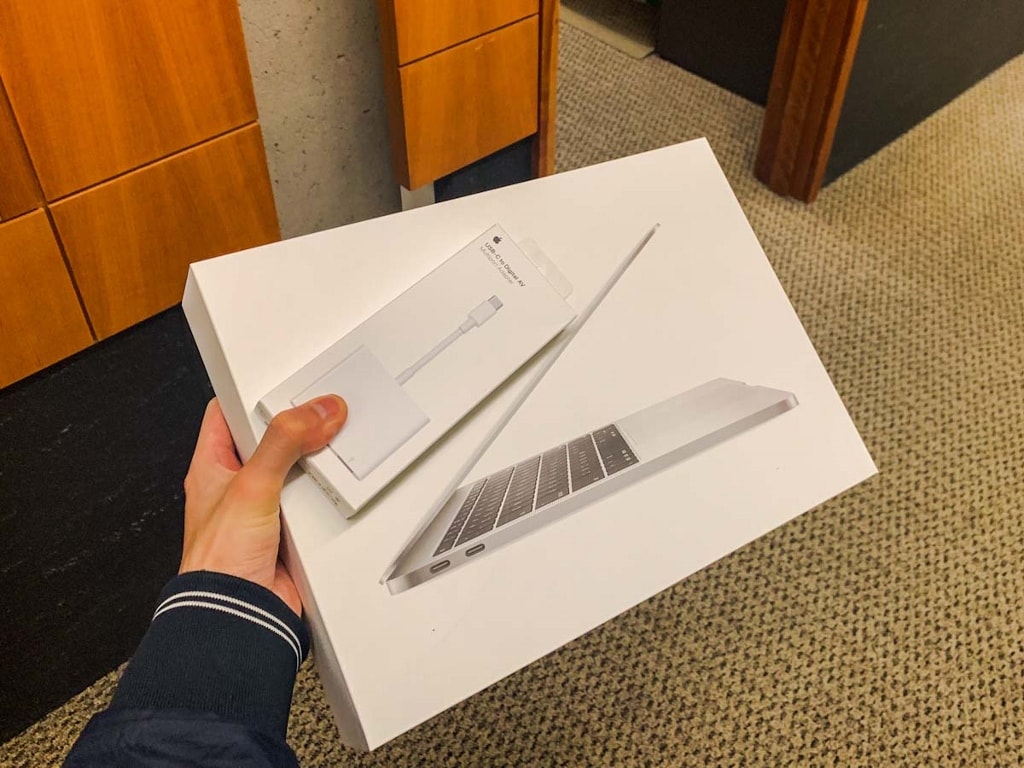
UW CSE 的 PhD 要约信中提到新入学的研究生都会获得一个免费电脑(有多种选择),我选了(标准选项里的)MacBook。这篇博文记录我初探 macOS 的事情。作为探索结果,我居然又给微软报了一个 bug!
Don’t f**king move selectable items upon selection!
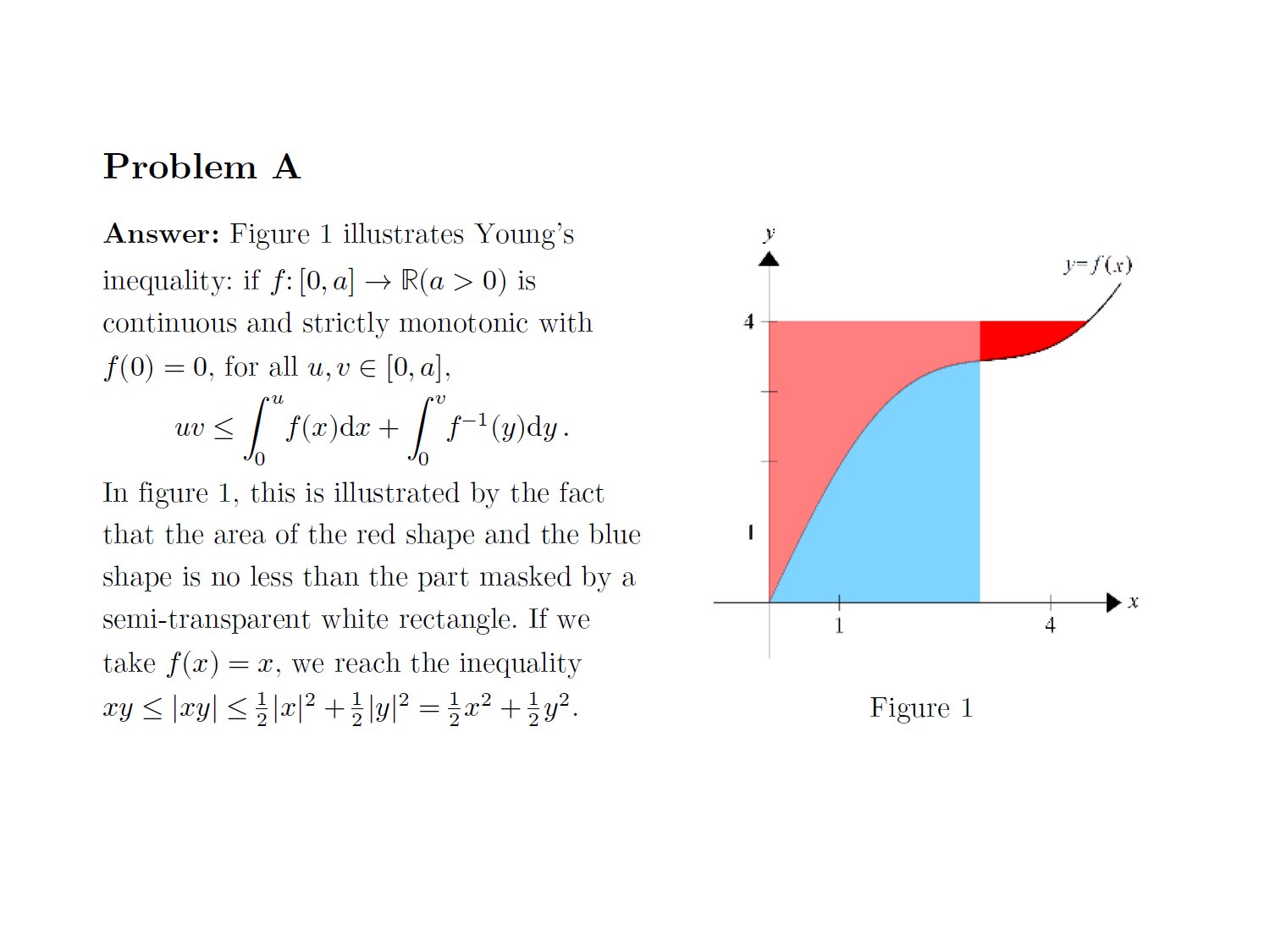
Nyuwa, the mother goddess of Chinese mythology, mends the sky according to an ancient Chinese legend. Today, Nyuwa is asked to mend the epigraph of a continuous function over an open set so that the function becomes convex. What can we say about this?

It is widely spoken that the Equation Editor of Word (OneNote / Office) is inferior and harder to use than LaTeX. While this is true for a hardcore user, a lot of people spreading the word aren’t really understanding the thing and are just parroting others. I suspect that for a lot of them, the ability to efficiently typeset beautiful mathematical formulae is limited by knowledge and carefulness. People don’t seem to care enough to learn and correctly employ the tools at hand.
Having received my MacBook Pro 13-inch, I started to alternate between my Surface Book and MacBook, to get used to macOS and keep everything synchronised. Today when I was transcribing my notes to OneNote, I noticed a rendering problem on the screen. Propaganda (from Apple fanboys) has it that macOS supports high DPI displays well (of course including its very own screen), it turns out the story isn’t as true as the propaganda claims. Later, it was revealed that the reason is font smoothing is on (by default for me), and turning it off resolves the problem.
Update: I misunderstood how the app was sideloaded. See my further investigation and I apologise for the wrong blames. Hands down! The usage is legitimate and a perfect example of installation on demand (advertisement). Embarrassingly bad is for myself.
I had a maths-related nightmare that (initially) was concerned about counting solutions of a linear equation modulo M with integral coefficients. Though the whole detail of the dream cannot be written down due to privacy reasons, at least I can write a simple introduction on solving this specific problem here. Update: An error in the original solution has been corrected. Another update the same day: The original solution is correct.
A commit to Ant Design, an enterprise-oriented open-source Web UI library by Ant Financial (蚂蚁金服), on 10 September 2018 buried an Easter egg for Christmas, which has caused a heck of havoc since Christmas. This entry also talks about not-so-obvious features in my blog.
我感恩节期间买了 Nintendo Switch,是为了玩 Pokémon Let's Go Pikachu,也就是《口袋妖怪·黄》的重制版,为此我还配上了 Pokéball Plus(配信梦幻的精灵球形状的遥控器,也可以作计步器用)。刚刚结束一周目(登入名人堂),写篇博文记录一下。

As a perfectionist, I have been struggling to have a perfect PIM (personal information management) solution. For the personal part, I currently use (Exchange-based) Outlook.com. For the professional (institutional) part, things have been so hard. This entry records some of the problems I have encountered so far, and for certain ones, a solution. Expect this entry to be a mess and full of complaints.
我的博客中第一次提到《铁甲小宝》是在《清华网络碎碎念:交费死锁》,最近我又在杂乱地复习它,发现了一些有趣的事情。本篇博文介绍这些内容,并记录一些备忘知识。

Sharing data among apps is a common task in modern operating system. Both iOS and Windows Runtime provides central means of transmitting data from one app to another beyond the clipboard. In this entry, I will look at the sharing functionalities in both systems.
这次 Microsoft 和 Apple 都令人恼火!
Group presentation is a method to express groups as a quotient of a free group and a normal subgroup. In a presentation, there are generators and relators, and the presentation yields a ‘minimalist implementation’ of these generators and relations. Some cases of special interests are finitely generated/related/presented groups. From the definition, finite generation + finite relation is not linguistically equivalent to finite presentation. There has been some discussion on the relation of the three properties for several other algebraic structures. This entry proves that finite generation + finite relation implies finite presentation for groups.
A brain teaser that remains open in Yao class WeChat group, up to the time of writing of this entry. See if it interests you and if you can solve it.
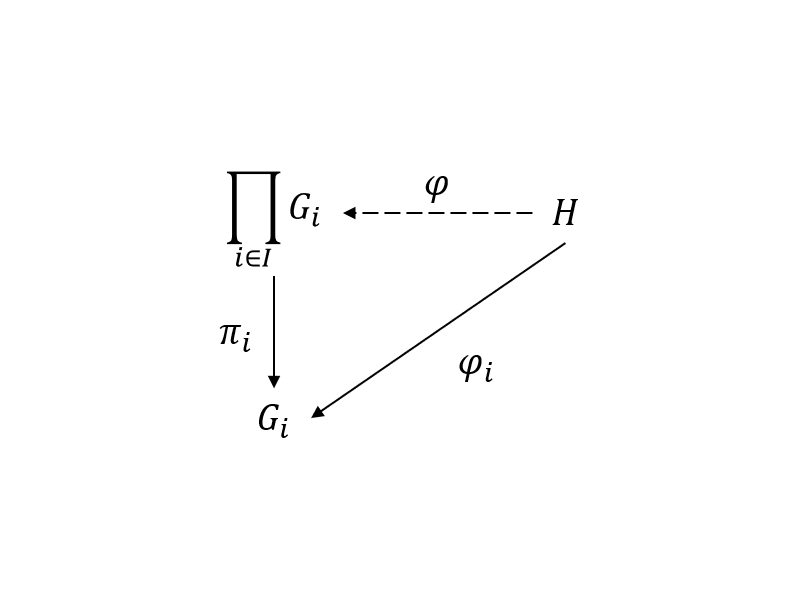
I’m taking an algebra course and regaining my algebra sense (non-sense?). Familiar to us is that direct products [resp. sums] of groups [resp. abelian groups] possess their versions of universal properties. When reviewing these things, I went curious on what would go wrong if the arrows were reversed. Let’s try and see.
Issue #6799 in PowerShell repository on GitHub raises the question why Previous Versions is opening previous versions of a directory in PowerShell, instead of File Explorer as expected. The reason is that PowerShell 6.1.0 (preview) installer creates a context menu to open the shell on any folder. However, it unfortunately names the verbs as open/runas, which is very dangerous since they are canonical and do not make much sense for a folder. Related is issue #7815, where shortcuts to a folder are opened in PowerShell.
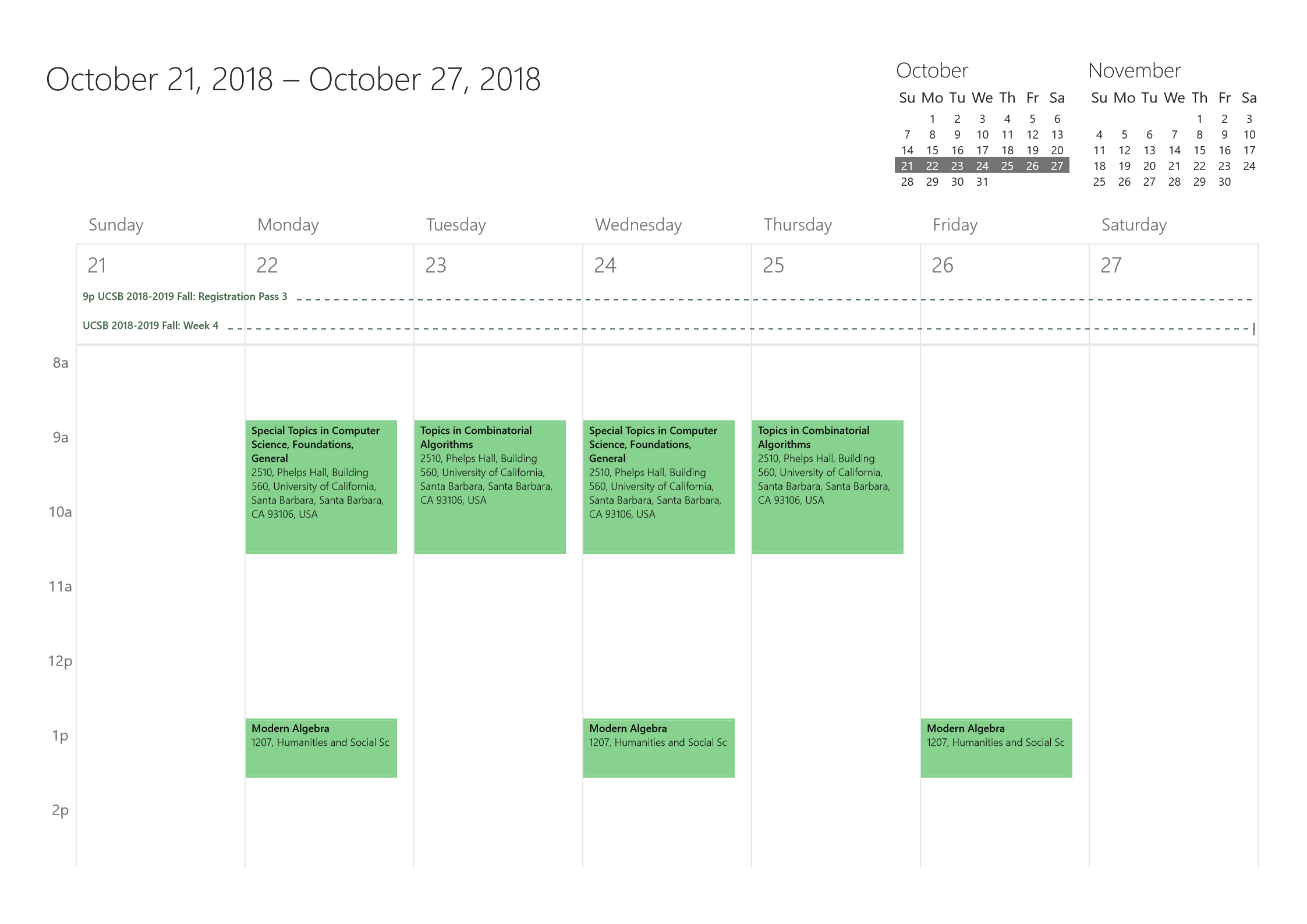
日历是一个很棒的时间管理工具,作为学生,一个常见的需求是把课程表导入日历。这就引出了好几个需要考虑的问题。我经过几个学期的摸索,实现了一个对自己完全够用的日历管理工具。
Outlook 2016 GUI always creates an event with at least one attendee, which makes Outlook.com and Outlook for iOS have difficulty correctly interpreting the appointment. Instead, they think it is a meeting. However, if you create the event with Outlook object model, there is a good chance the event is created neatly. In addition, events created on Outlook.com or in Outlook for iOS are always neat.
Continuing ‘Hosting a preview handler in WPF, part 1: UI and file associations’, we will do the major COM interop in this entry. Many people have failed to host the handler correctly because of careless implementation, so look carefully! Also, we will demonstrate some broken preview handlers, including ‘Adobe PDF Preview Handler for Vista’, ‘Microsoft Word previewer’ and ‘Microsoft PowerPoint previewer’.
一回想过去,就很容易觉得生命都过得不够充实。今天早晨偶然想要看一下自己的原来的卧室,感觉就上来了。
As a fanboy of Raymond Chen, I’m always intrigued by Windows Shell. After his three interesting examples of Reading a Contract From the Other Side, I decided to write one myself. Our victim is Preview Handlers and Shell Preview Host. Today’s entry will prepare UI and file association information retrieval for our little program.
微博校园发了一个转得都“变质”的考试附加题照片——还有可能是 PS 的!那些字真的跟纹身刚刚纹上去的时候一样,底下还泛红。我把这个题做了一做,又苦于最近没什么新的博文主题,就暂且写一篇这个罢了。
我之前在知乎问题“为什么很多人要禁止 Windows 10 自动更新”下多个回答的评论区宣传 ShutdownBlockReasonCreate 这个 API,尝试“教育”开发者正确处(阻)理(止)Windows 10 自动更新重启带来的关键任务被终止的问题,还因为这个被人挂了。一开始我抱着怀疑的态度提出的方法,之后不知什么原因就假设这个 API 确实有效了——我当时已经知道该 API 不能其效果的情况,但是我没料到“大更新”的时候 Windows 真的会用那么暴力的方法重启电脑。本文记录了一些我的观察,并从使用者的角度给出一些关于 Windows 10 自动更新处理上的建议。
A curious problem I encountered when using Windows PowerShell to backup my Outlook signatures.
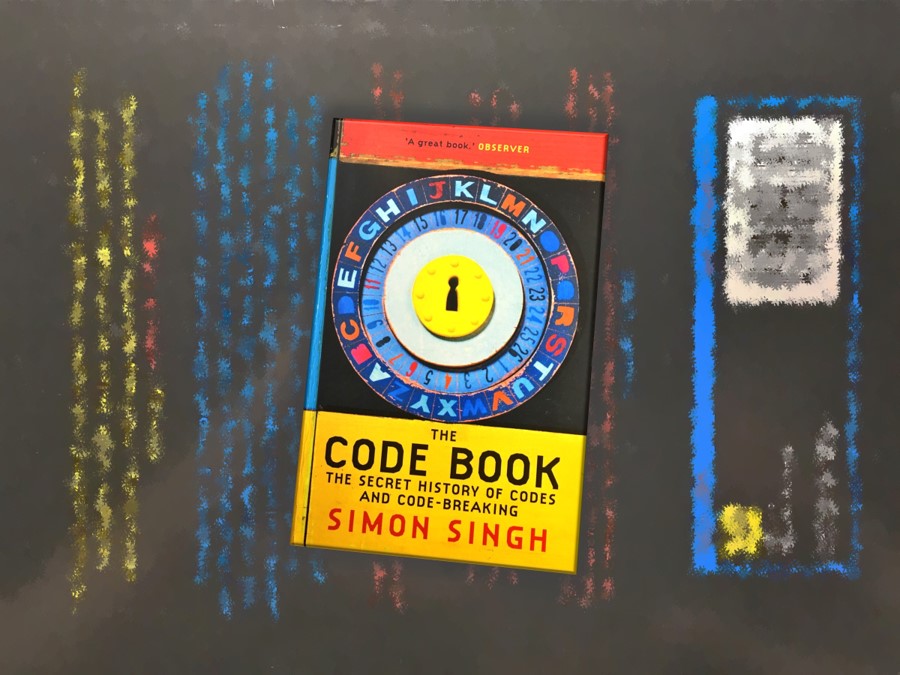
操作系统课中讲安全的一节是代课老师上的,期间他推荐了 The Code Book (Simon Singh) 这本书,说是讲密码学历史的。我对密码学感兴趣,就读了一读,并照“不动笔墨不读书”的原则,记了读书笔记,发表出来以飨观众。
本系列旨在忠实提供 1980 版的《悲惨世界》概念版音乐剧的歌词。第七篇记录的是 Valjean chez les Thénardier 和 La valse de la fourberie 的歌词。自此,第一幕结束。
交叉信息研究院的本科生操作系统课程的大作业很奇特,并不是 4 个 NachOS 作业,而是两次 NachOS、两次分布式数据库。最后一次大作业是要写一个 Bitcoin 挖矿程序,而且还有组间比赛,各个小组的矿机和客户端会一起运行一段时间,最终获得最高手续费的矿机会获胜。

Have you ever tried using UseNewEnvironment switch when invoking Start-Process cmdlet? Intuitively, turning it on makes the newly created process use the default environment instead of that of the parent process. However, its semantics is way more complicated, obscure and buggy than the intuition. TL; DR: You rarely want to use this switch.
The UAC Consent UI is rather involved in how it creates an elevated process, and it likes fooling around with process identifiers.
Jinhao Zhao was making up problems for some OIers. Let’s see this maths problem!
我觉得这是我参加的第 3 次 hackathon,并且是第 2 次 intensive hackathon。还是挺有意思的,记录,以飨。

The developer (Microsoft, this time) created a shortcut before it should have been.

Someone wanted to know how to create a file that denies itself from being removed, yet found he could still remove the file even denying DELETE access from Everyone. The reason is that there is DELETE_CHILD access on its containing directory. How does this relate to ‘the directory is not empty’?
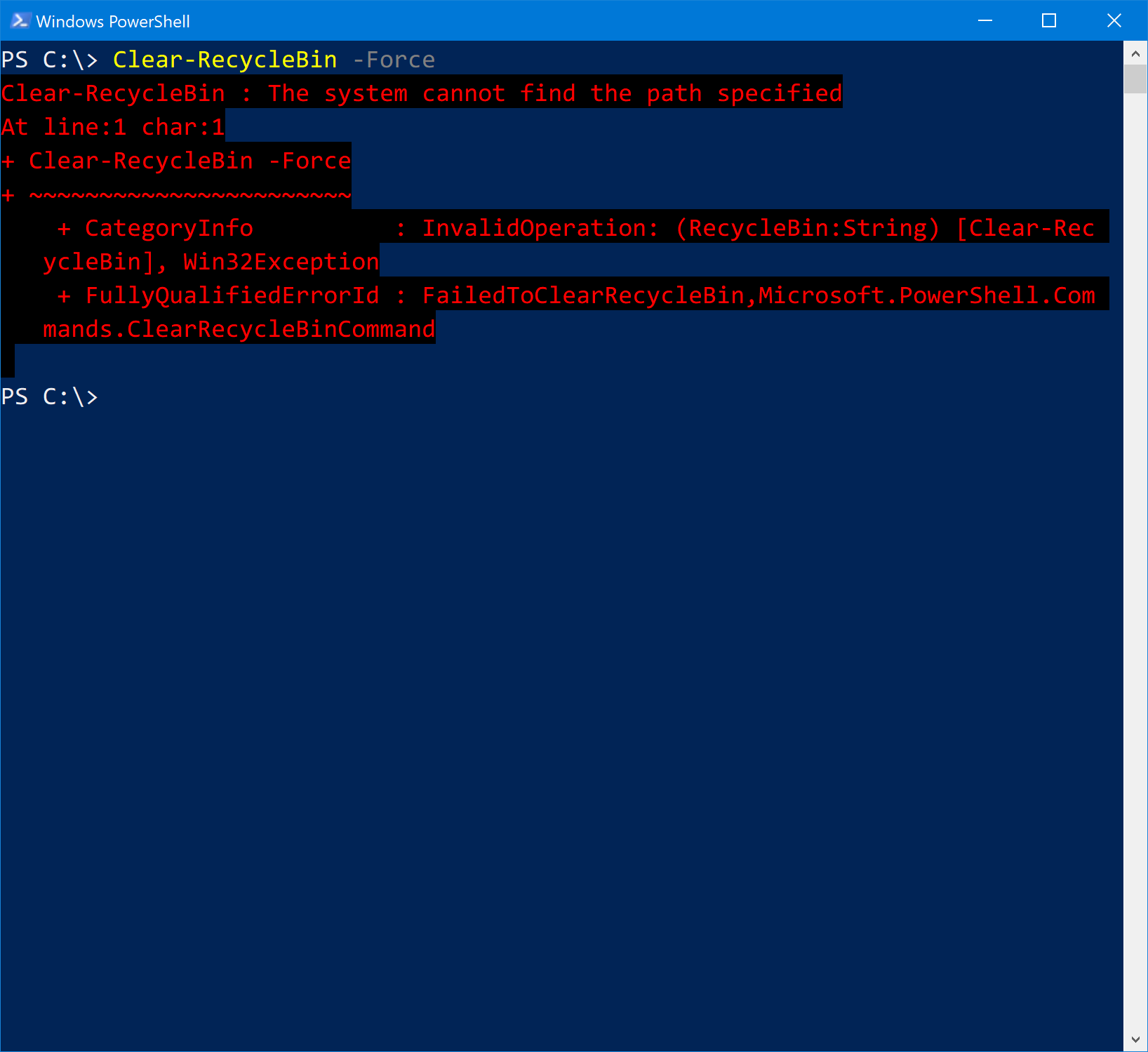
Clear-RecycleBin is a cmdlet that clears your recycle bin. Internally, it calls SHEmptyRecycleBin function. It has been malfunctioning for a long time: when you run the cmdlet for the first time in a PowerShell session with Force switch on, it produces an ErrorRecord. Further investigation shows that it is detecting error status of SHEmptyRecycleBin the wrong way. To make things worse, SHEmptyRecycleBin is really bad at error handling.
两个小发现:Invoke-RestMethod 真的很好用;微软大法好!好吧,其实前一个也是“微软大法好”的一部分。
High Contrast theme that is great for daily use, with extra large cursor. Updated one year later: I created a theme that can be used to simulate Windows Standard. Check it out!
本系列旨在忠实提供 1980 版的《悲惨世界》概念版音乐剧的歌词。第六篇记录的是 Au sergent de Waterloo 和 La devise du cabaretier 的歌词。
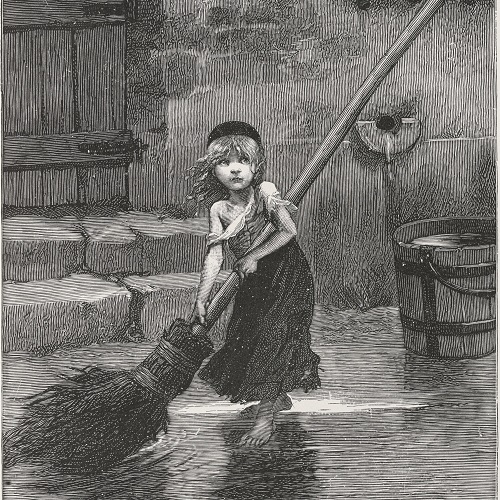
本系列旨在忠实提供 1980 版的《悲惨世界》概念版音乐剧的歌词。第五篇记录的是 La mort de Fantine、Mon prince est en chemin 和 Mam'zelle Crapaud 的歌词。
本系列旨在忠实提供 1980 版的《悲惨世界》概念版音乐剧的歌词。第四篇记录的是 Fantine et Monsieur Madeleine、Monsieur Fauchelevent 和 Comment faire 的歌词。
a.k.a. How to be disappointed again by UA. I was visiting New York University and Carnegie Mellon University. Flying from Beijing to New York, from New York to Pittsburgh, from Pittsburgh to Beijing via Chicago, I chose United Airlines, one that suffers from previous scandals on ‘violently reaccomodating a customer’. It turns out that their in-flight entertainment system is also torturing! This entry was written during the flight from Chicago to Beijing.
本系列旨在忠实提供 1980 版的《悲惨世界》概念版音乐剧的歌词。第三篇记录的是 J'avais rêvé d'une autre vie、Fantine et Monsieur Bamatabois 和 Dites-moi ce qui se passe 的歌词。
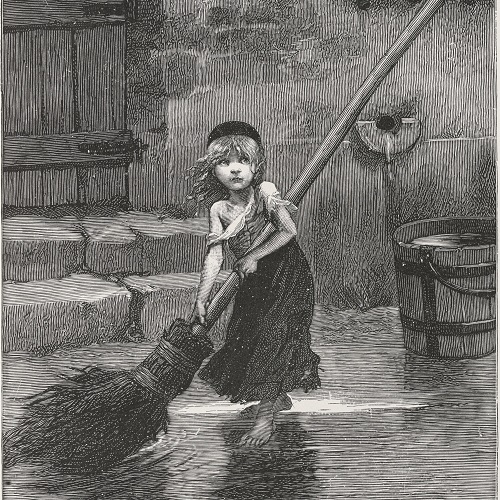
本系列旨在忠实提供 1980 版的《悲惨世界》概念版音乐剧的歌词。第二篇记录的是 L'air de la misère 和 La nuit 的歌词,其中后者包括 Les beaux cheveux que voilà。
本系列旨在忠实提供 1980 版的《悲惨世界》概念版音乐剧的歌词,目标是无误地提供歌词,即使网络上已经有歌词的,我也会和 1980 版的现场录音以及专辑版录音比对。第一篇记录的是 Tant qu'il existera 和 La journée est finie 的歌词。
Continuing the last entry. I wrote a reducer of lambda terms (normal order, call-by-need).
I have heard about λ-calculus as a computational model for long, but never got a chance to have an even recreational look at it. Today’s entry simply records the creating of the parser.
When you open VS2015 Command Prompt from a newly installed instance of Visual Studio 2017 Community, the prompt fails to initialise the variables. Telling you to ‘make sure either Visual Studio or C++ Build SKU is installed’. Searching the Internet, this seems to be a known and persisting issue. Here I propose an elegant workaround for it.
Base conversion is the conversion between notations of number, and NOT the numbers themselves. I discuss a common mistake on methods of base conversion, and a common mistake in thinking about ‘base conversion’ in computer programs.
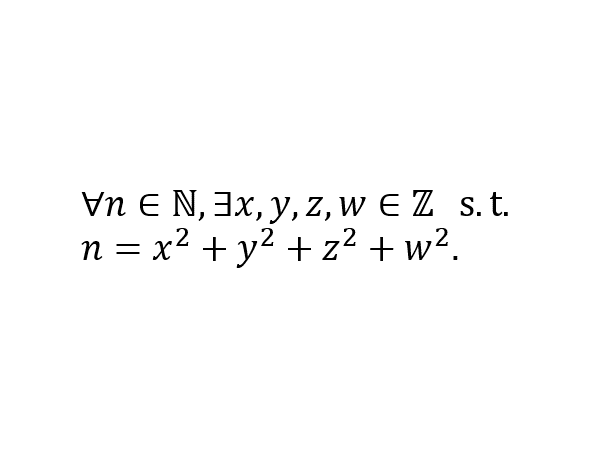
Lagrange’s four-square theorem is a beautiful result in number theory. However, to the best of my knowledge, I haven’t encountered it often in theoretical computer science. Today’s entry discusses two interesting stories related to this theorem.
姚栋想要知道如何在 Windows 中使用命令解压缩 ZIP 文件夹。他表示如果要用 .NET Framework 提供的 API,则需要 4.5,但环境要求 4.0;如果用 PowerShell Expand-Archive 命令,则需要 5.1,但环境只允许 2.0;想用 cmd,但不知道怎么做。然而应该时刻记住:Windows 自带的 GUI 实际上经常是 COM 的图形版,在 COM 中寻找几乎总是可以找到你想要的图形操作的命令版本。
Starting from the classic puzzles of finding patterns in a sequence, this entry explores the framework to define persuasive patterns. The framework is found to be quite self-contained in the sense that it is ‘asymptotically invariant’ to the choice of ‘language of expression’. The only short-coming of this framework is that it works only for computable sequences, yet the process of pattern discovery is uncomputable.
In this entry, I discuss a pathological construction of general terms of a class of integer-valued sequences with the widely accepted concept of ‘elementary functions’. The idea here is to simply ‘concatenate’ the integers in a real number, then extract the appropriate digits for each term. It turns out that this definition characterises the elementariness very well (note that the definition is also self-referencing). The extended inspection leaves a problem open: Are all integer-valued sequences elementary? Update: The question is solved with an affirmative answer.
In this entry, I discuss a kind of widely posed exam problems for elementary calculus learners. It concerns a technique of application of (differential) mean value theorems. Specifically, a class of such problems can be solved dogmatically if the equation to prove resembles a ‘factorisable’ linear differential equation.

I allowed myself some CHANEL products to ‘reward’ myself for the acceptance of my first cryptography paper. I also consider spending money at its best value an interesting game. A commonly-seen discount aux Galeries Lafayette Xidan (Beijing) leads to an obviously NP-complete problem. Haha!

An algorithmic imagination of how Sina Weibo could implement Frequented Visitees, a feature that gives users the serveral accounts which they visit the most often.
在 Aarhus 的密码学研究从春天到秋天一直断断续续在进行。今日传来喜讯:我们的文章已被 PKC 2018 接收。
我学习过程中一些关于代数数的说明。
去听习题课并不是为了听讲习题,而是为了混参与分数(虽然我相信这个课不用参与分数也可以拿很高的分)。虽然,仍然有两则有趣的见闻以飨观众。
首战 GRE 不战而败,首战 TOEFL 可以算是“凯旋归来”吧!第二次战 GRE,感觉稳了。
这其实是一篇汉语文章,标题的意思是:“我刚刚安装了更新(iOS 11)。”用法语写标题是因为我的 iPhone 语言设置为法语了。谈谈我初步发现的几个小变化。
Groove Music allows the user to store their music collection, including songs available via Music Pass subscription, those purchased from the Store, those stored on your OneDrive and those stored locally. This gives the users false impression that purchased music are secured by Microsoft’s service so they’re never lost.
其实也不是洗澡的时候想的,是睡不着的时候想的。想完了,查一查文献,姚先生已经做了。
清华网络费用非常高!另外,曾经清华网费有死锁,因为使用了网银;后来采用了微信、支付宝,声称解决了死锁。但我今天一试,发现根本不是这样的!(已更新)

2017 年 8 月 17 日,一条消息引爆了小范围清华人的朋友圈——大礼堂前的日晷被人刻字了!我特地前去观摩,并拍下了照片,可稍后再去的人却发现,刻上去的字被磨掉了。

我发现当我的生活充实的时候就有有趣的 blog 可以写!因为一忙起来,就要忙里偷闲,然后就会胡思乱想,然后就可能有有意思的东西。(已更新)
正在转战 C++ 写密码学代码,然后突然想温习一下多重继承、虚拟继承,熟知公有虚拟继承是 C++ 实现“接口”语义的成语(idiom,惯用法);思想游荡到了 C♯ 的世界,CLR 也支持接口,而且 C♯ 还有一个为人称道的显式接口实现(有一半私有虚拟继承的感觉),但是这里面隐藏了一个小“坑”……
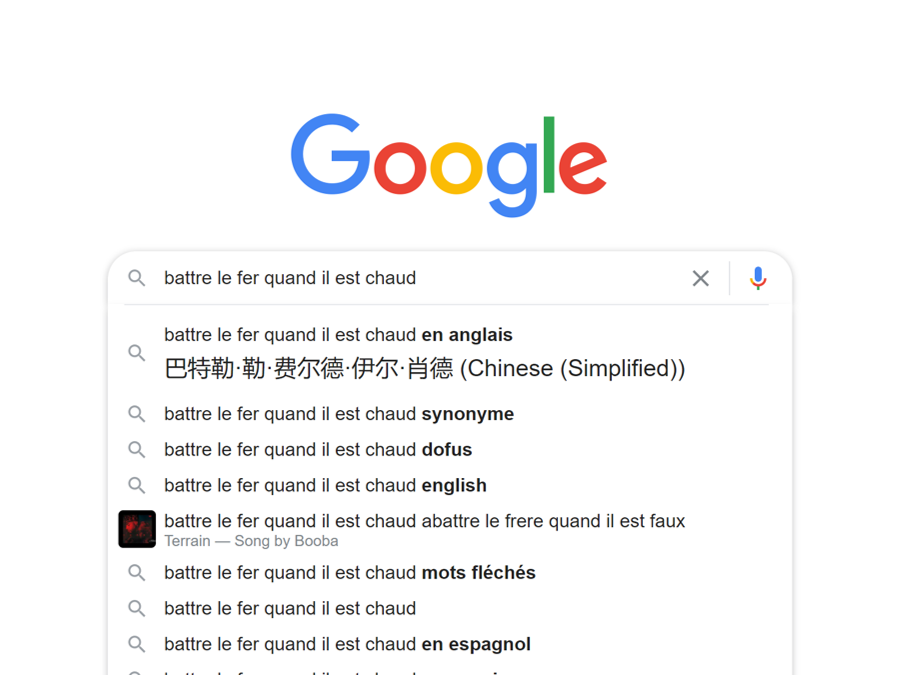
This entry explores an interesting case of CRTP (curiously recurring template pattern) in C♯ that allows us to use operators. The other topic is elegant implementation of generic parameters that are (semantically) values instead of types.
强行应用一下“金融工程导论”课程的知识:用无套利定价理论考虑买断软件的价格。
如何背叛“微软教”。7 月 24 日更新:我的一个好朋友也要换手机了!
第一次长居国外。本篇已完结。

Let me explain the classic idea that ‘the algorithm of a crypto system should be considered and made public’ to you. Particularly, I will discuss what it means by ‘crypto system’, which tells us what information should be no secret at all.
接待我妈可是非常累的,因为她太能走路了。我在她的强行旅游意愿下成功地走马观花了一番哥本哈根、奥胡斯、巴黎。

数学文字中有很多“一般”,例如“一般地”、“不失一般性”,还有“特别地”等说法,它们的意思和日常中的“一般来说”可大不相同。
One more step towards accessible Web.
I should have honoured myself as a bug trigger.

A classic trick of backward references but painfully slow. And some comments on benchmarking JavaScript code.
When Exchange freaks out, I talk to Microsoft. Case closed.

A practical problem I encountered in 2016, which I insisted on implementing with pure CSS as long as it was possible. At first it was solved with mathematical logic tricks but later it turned out there was a much simpler solution.
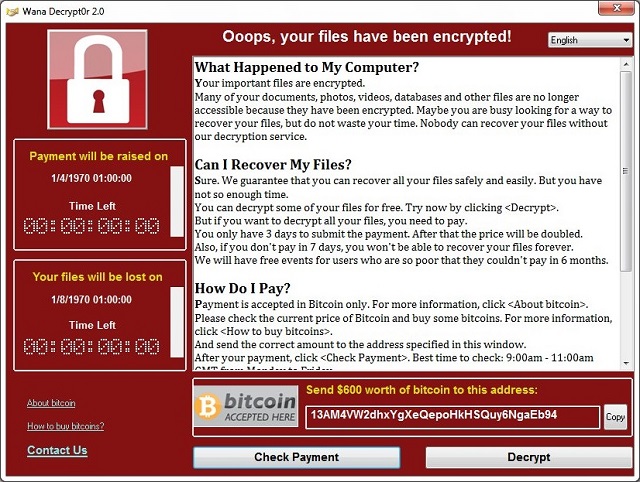
又一次病毒爆发。
How do you localise ‘Filter’ button for Mainland China?
‘Clip to OneNote’, explained.
第一次主动参观艺术展览,觉得很有意思。小心:本文将会耗费大量流量!

Inheriting the wrong value?

I think Internet Explorer wins this time.

Learn the meaning of different gestures, buttons and hotkeys to ‘close’ Windows Store apps. And you have to learn it by heart like French conjugation.
And those APIs are specially designed for Edge (and modern IE) to enable Live Tile experience when the site is pinned to Start.

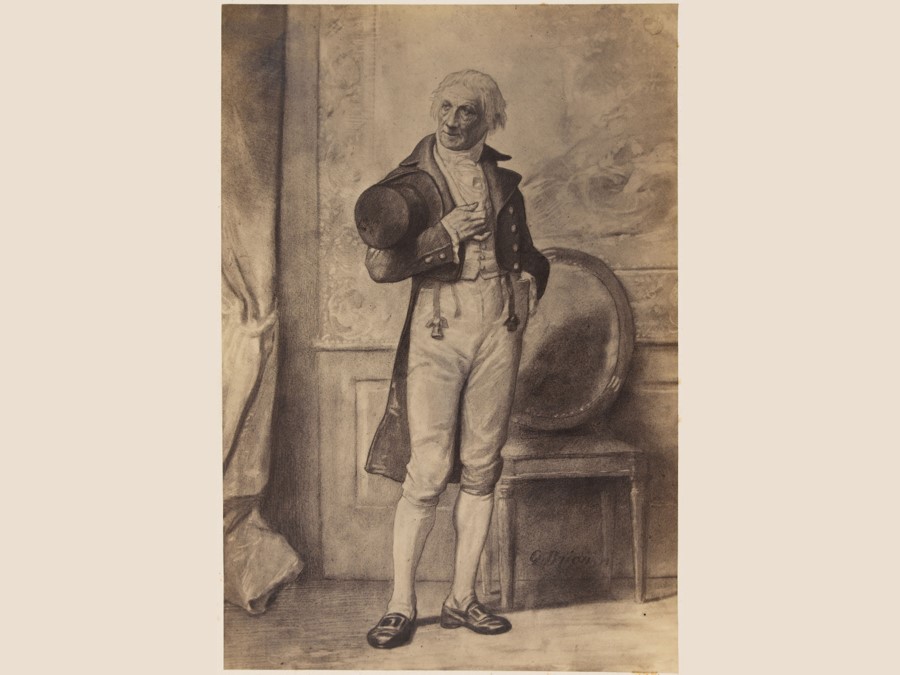
第一次进入法国,第一次去巴黎,第一次参加《悲惨世界》现场音乐会。更重要的,第一次说走就走的旅行。

When Microsoft removes a useful thing.

One of the issues I encountered when I was at Jisuanke. Emulating is the point.
A better Windows Phone.
知乎药丸。另外该列表持续更新。

Sometimes you have to explain the name of a functionality.

Something does not behave as desired on IE.
Sequential is sequential, dependency should be respected.
回归的功能有很多,也不乏新功能和改进。

它的语义不等价于 std::function<TReturn(TArgs...)>。
Write some simple calls to multiple-window APIs.
Introducing multiple-window universal Windows apps.
一篇流水账,你可以叫它“意识流”。
我倾向于认为答案是 1。

“回”“老家”四川对我来说是一种负担,我想回老家——回北京。
I was participating Advanced Assessment for Admission (AAA) of Tsinghua Union, passed the first phase and was interviewed by Insititute for Interdisciplinary Information Sciences of Tsinghua University. Here is a transcript of the interview.

我参加了“华约”(清华大学联盟)的自主招生(AAA,或“高水平大学自主选拔学业能力测试”)。我通过了初试并被清华大学交叉信息研究院面试。这是一份面试的转录。

My first blog entry.